Cybersecurity is the practice of protecting computers, networks, devices, data, and systems from unauthorized or malicious access, attacks, or damage. Cybersecurity aims to ensure the CIA of information and resources in the digital world.
Cybersecurity covers various domains and aspects, such as:
- network security
- application security
- information security
- operational security
- disaster recovery
- end-user education
Cybersecurity also involves different types of threats and attacks, such as malware, phishing, ransomware, denial-of-service, and advanced persistent threats.
What’s CIA in here?
Confidentiality: Prevent or minimize unauthorized access to data while in storage, in process, and in transit.
Attacks:
- Stealing password files
- Social engineering
- Port scanning
- Eavesdropping
- Failing to fully authenticate a remote system before transferring data
- Walking away from an access terminal while data is displayed on the monitor
Countermeasures:
- Encryption at rest (whole disk, database), in transit (IPSec, SSL)
- Strict access control
- Rigorous authentication procedures
- Clean desk policy
Integrity: The quality or state of being whole, complete, and uncorrupted.
Attacks:
- Viruses
- Logic bombs
- Unauthorized access
- System backdoor
- Faulty programming
Countermeasures:
- Hash total verification
- Configuration management
- Interface restrictions
- Extensive personnel training
Availability: Authorized subjects granted timely and uninterrupted access to objects.
Attacks:
- DoS attacks
- Communications interruptions
- Accidentally deleting files
Countermeasures:
- Firewalls and routers to prevent DoS attacks
- Maintaining and testing backup systems
- Implementing redundancy for critical systems
Every organization has unique security requirements. And, importance of CIA is different. In general, military and government organizations tend to prioritize confidentiality above integrity and availability, whereas private companies tend to prioritize availability above confidentiality and integrity.
IAAA Principle:
The cybersecurity framework focused on access management:
-
Identification: An identity is a piece of information that distinguishes one entity from another. A common form of identify is a username which is used in the authorization process when you log in. Once logged in it is your username which can be used to track and identity your activity.
-
Authentication: where a user provides proof that he or she is who he or she really is. Multiple ways:
- Something a user knows (e.g password)
- Something a user has (e.g. hardware access token)
- Something a user is/does (e.g. fingerprint, retinal scan)
- Somewhere you are (e.g. office, city, country)
-
Authorization: the assurance that the user or the computer has been authorized to be granted access to specific information. Authorization is the policy that dictates access rights to assets and resources. Access control models that systems employ to manage the process such as:
- Discretionary Access Control (DAC): managed by owner of individual resources
- Mandatory Access Control (MAC): requires user clearance and file classification level to match
- Role-based Access Control (RBAC): requires group based role to inherit access rights
- Attribute-based Access Control (ABAC): requires a number of attributes to be met to gain access
-
Accountability: when a control provides assurance that all activities can be linked to attributed to a certain person or a process
also:
-
Auditing: programmatic means of tracking and recording actions for the purpose of holding the subject accountable for the actions while authenticated on a system
-
Non-repudiation: the assurance that someone cannot deny the validity of something
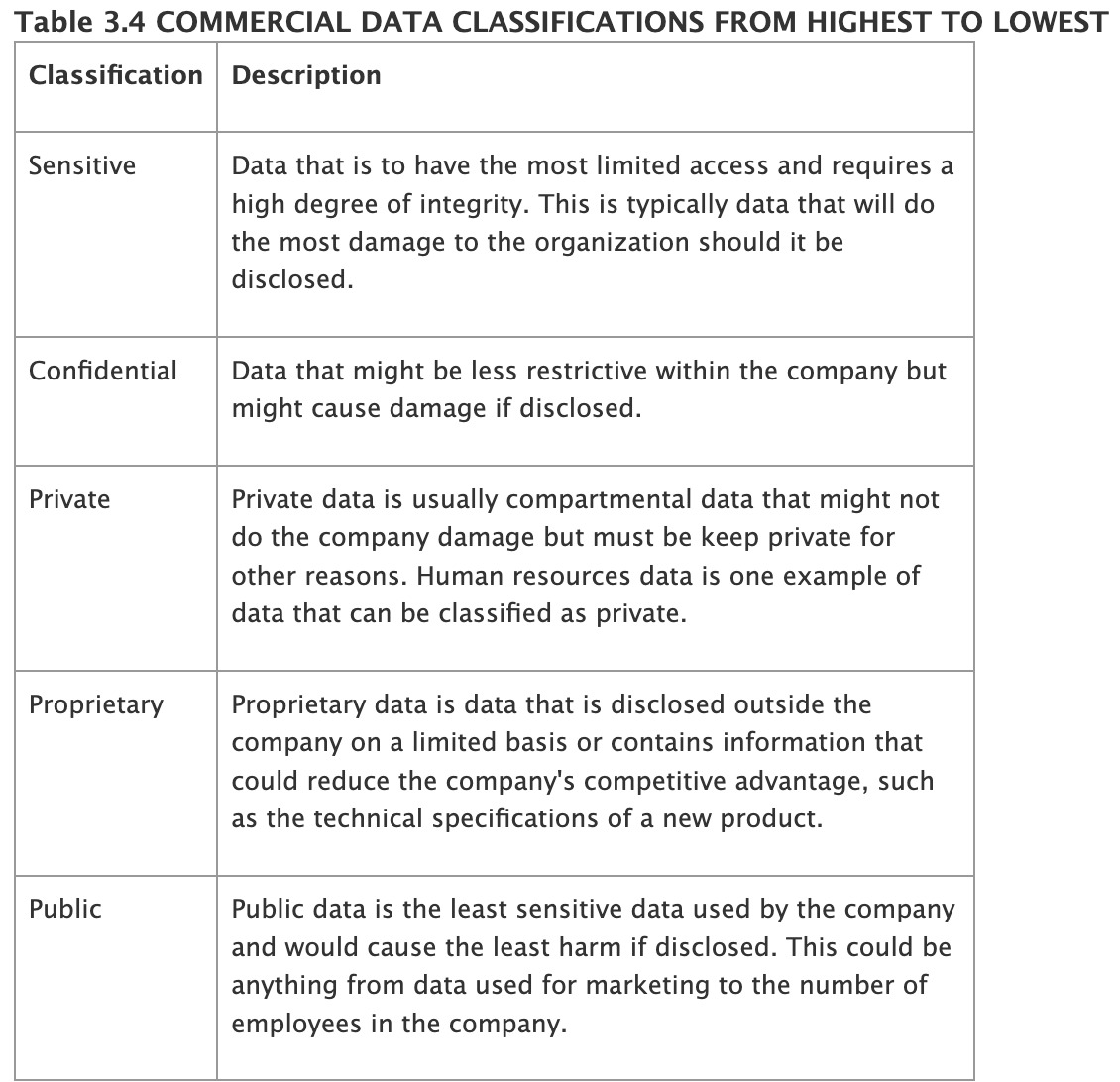
Defense in depth:
 Defense in depth is a concept in information security in which multiple layers of security controls (defenses) are placed throughout an information technology (IT) system. The idea behind the defense in depth is to defend a system against a particular attack using several independent methods.
Defense in depth is a concept in information security in which multiple layers of security controls (defenses) are placed throughout an information technology (IT) system. The idea behind the defense in depth is to defend a system against a particular attack using several independent methods.
In the following scenario a web browser is developed using defense in depth -
- the browser developers receive security training
- the codebase is checked automatically using security analysis tools
- the browser is regularly audited by an internal security team
- … is occasionally audited by an external security team
- … is executed inside a sandbox
Specialized area of security:
Physical security - strategies to protect people, physical assets, and the workplace from fire, unauthorized access, and natural disasters.
- Biometrics, Fence, CCTV, Fire extinguisher
Personal security - protection of the people within the organization.
- Evacuation plan, Floor warden
Operations security - ensuring business to run without interruption or compromise.
- Business continuity plan (BRP) and Disaster recovery plan (DRP)
Communications security - protection of communications media, technology, and content, and its ability to use these tools to achieve the organization’s objectives.
- Encryption
Network security - the protection of an organization’s data networking devices, connections, and contest, and the ability to use that network to accomplish the organization’s data communication functions.
- Firewall, IPS/IDS, DMZ
Information security (InfoSec) -
Impacts of cyber attacks:
Reputational damage, financial loss, loss of customers, drop of stocks and profits, loss of sales.
Security threats and vulnerabilities
A security threat is anything that could exploit a vulnerability, which is a flaw or weakness in an asset’s design, implementation or operation and management. A security threat can be malicious actor, such as a hacker, a virus, a worm, or a ransomware, or a natural event, such as a fire, a flood, or an earthquake.
A security vulnerability is a gap or loophole in an asset’s security that can be exploited by a threat. An asset can be anything of value to an organization such as a system, a data or a person.
For example, you have a house with a lock on the door. The lock is designed to prevent unauthorized access to your house. However, the lock has a flaw that allows anyone with a certain type of key to open it. This flaw is a vulnerability in your house’s security. A thief who has that type of key is a threat to your house. If the thief uses the key to open the lock and enter your house, he or she has exploited the vulnerability.
Risk is the potential for loss or damage when the threat occurs and exploits the vulnerability. The level of risk depends on the likelihood and impact of the threat and the vulnerability.
For example, if the thief with the key is very far away from your house and has no intention of coming near it, the likelihood of the threat is low and so is the risk. However, if the thief knows where you live and plans to rob you soon, the likelihood of the threat is high and so is the risk. To reduce the risk, you can either reduce the threat or reduce the vulnerability.
Risk management:
is the process of discovering and assessing the risks of an organization’s operations and determining how those risks can be controlled or mitigated. The goal is to reduce risk to acceptance level.
To reduce risk, an organization must
- know itself and
- know its adversaries
Know itself: managers from all three communities of interest (infosec, IT, business/non-technical)
- identify what resources are available
- understand how the organization’s information is processed, stored, and transmitted
- must locate the weaknesses of their organization’s operations
Know the enemy: identify, examine, and understand the threats facing the organization’s information assets, for example, threats to web app include XSS, SQL injection, DoS, CSRF etc.
-
Risk identification:
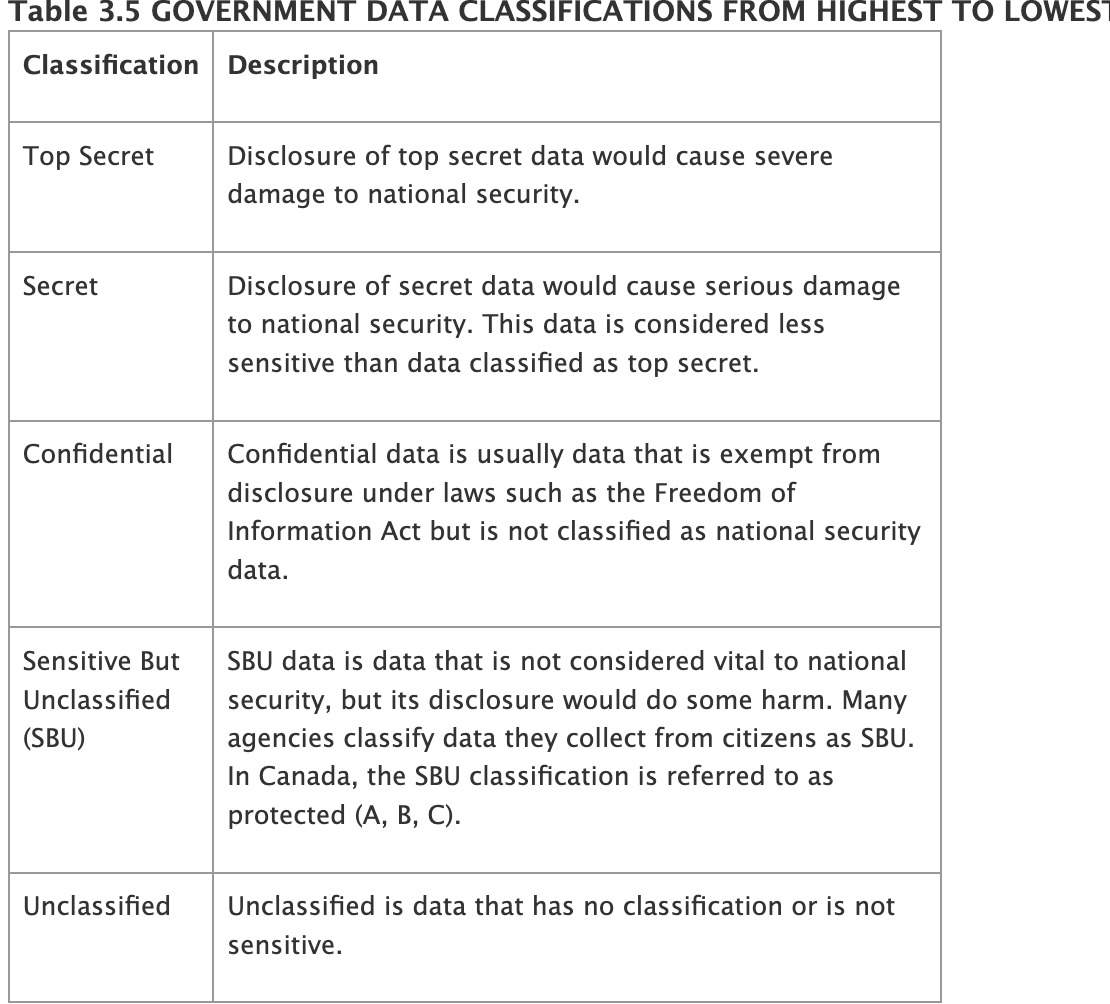
- begins with the process of self-examination
- identify the organization’s assets, classify them into useful groups, and prioritize then by their overall importance
- creating an inventory of information assets
- classifying and organizing those assets meaningfully
- assigning a value to each information asset
- identifying threats to the cataloged assets
- pinpointing vulnerable assets by tying specific threats to specific assets
-
Risk analysis:
- determine likelihood: for each threat-vulnerability pair, estimate the likelihood of the threat exploiting the vulnerability, using the predefined scale
- determine impact: estimate the potential impact if the threat were to exploit the vulnerability, using the predefined scale
- calculate risk levels: multiply the likelihood and impact for each threat vulnerability pairs to calculate the risk level
- quantitative (AV, EF, SLE, ARO, ALE) vs qualitative risk analysis (Brainstorming, delphi, focus, surveys)
-
Risk evaluation (can be part of risk analysis):
- list analyzed risks
- apply risk acceptance criteria
- categorize risks
- techniques (probability impact matrices, risk scoring, risk mapping, monte carlo simuation)
-
Risk treatment/control/response
- analyzes and implements possible responses to control risk: risk avoidance, risk transference, risk mitigation and risk acceptance
- control mechanism: technical, administrative, physical
- scoping and tailoring - SCA testing or evaluation of controls to determine extent to which controls are implemented correctly
-
Risk review/monitoring
- process of evaluating the updating the risk management plan on new information or changes in the environment
- involves updating the risk resister or report with latest information and status of the risks and communicating the results and recommendations to the relevant stakeholders
- techniques: key performance indicators, key risk indicators, audits, reviews, reports,
- the goal of information security is not to bring residual risk to zero, but to bring it in line with an organization’s risk appetite
The remaining risk that has not been completely removed, shifted, or planned for, after vulnerabilities have been controlled as much as possible
- Residual risk = Total risk - control gap
- Total risk = threats x vulnerabilities x asset value
Due care and due diligence:
Due care is doing what a reasonable person would do in a given situation.
- the prudent man rule.
- due care is developing a formalized security structure containing a security policy, standards, baselines, guidelines, and procedures.
- failing in due-care is negligence, a legal offense.
- Example: CEO has the duty to protect their organization
Due diligence is the management of due care.
- a step beyond due care
- Example: background checks on employees, risk assessment of physical systems, testing backup services, etc.
Risk management framework:
Risk management framework is a guideline or recipe for how risk is to be assessed, resolved and monitored.
Eg: ISO/IEC 27005 and NIST RMF
categorize information system → select security controls → implement SC → assess SC → authorize IS → monitor SC
(policies coming up later)
Malware and cyber attacks
Malware is a term that refers to any malicious software that is designed to harm or exploit a computer, device, network, or user.
- Email Attachments/Links (Emotet, Trickbot, and Dridex)
- Network – Vulnerable ports and services (WannaCry, NotPetya, and Conficker)
- Web – Code Embeds and Redirects (Zeus, Angler, and RIG)
- Removable media (Stuxnet, Flame, and BadUSB)
- Torrent downloads (CLoader, CryptoLocker, and TorrentLocker)
Virus
Definition: Malicious programs that attach themselves to legitimate programs or files. When these programs or files are executed, the virus becomes active, replicates itself by modifying other computer programs and inserting its own code into those programs. Computer viruses generally require a host program. The virus writes its own code into the host program. When the program runs, the written virus program is executed first, causing infection and damage.
Function:
- Propagation: The process by which a virus spreads from one system to another, infecting machines along the way
- Destruction: The virus executes its malicious payload, which could range from deleting or modifying data to corrupting files or displaying messages.
Example: A notable example is I love you virus created by Onel de Guzman in May 2000. It spread through emails, appearing as a harmless text file due to hidden extensions in Windows. It caused significant damage globally infecting over 10 million computers.
Propagation techniques:
- Master Boot Record (MBR) viruses: Target the MBR of bootable media to load the virus during the system’s boot process. They often spread through infected media. An example is the Petya ransomware.
- File infector viruses: Infect executable files (.COM, .EXE) and activate when these files are run. They can range from highly destructive to benign in their actions.
- Macro viruses: Utilize the scripting functionalities of applications (e.g., VBA in Microsoft Office) to execute malicious code. The Melissa virus is a notable example.
- Service injection viruses: Infect systems by injecting malicious code into trusted OS runtime processes, evading detection by antivirus software.
Virus technologies:
-
Multipartite: Combines multiple propagation techniques for infection. For example, the Marzia virus infected critical system files like COM and EXE files initially, then later wrote malicious code to the system’s master boot record (MBR), transforming into an MBR virus. This technique enhances the categorizedvirus’s ability to spread and cause damage by exploiting different vulnerabilities within a system.
-
Stealth: Conceals themselves by tampering with the operating system to deceive antivirus software. For instance, a stealth boot sector virus may overwrite the system’s master boot record with malicious code and modify the operating system’s file access functionality to cover its tracks. This makes it challenging for antivirus programs to detect and remove the virus.
-
Polymorphic: Alters its own code to evade detection while keeping its malicious functionality. While their propagation and destruction techniques remain the same, the virus’s signature changes each time it infects a new system. This dynamic behavior makes it difficult for antivirus software to detect and combat polymorphic viruses effectively.
-
Encrypted: Encrypted viruses use cryptographic techniques to obfuscate their payloads, making detection more challenging. By encrypting their code, these viruses aim to evade detection by antivirus software. However, the virus decryption routines often contain identifiable signatures, which antivirus programs can use to detect and neutralize the virus.
Worms
Definition: A type of malware that replicates itself to spread to other computers, often exploiting vulnerabilities in software or network security. Unlike viruses, worms do not need to attach themselves to an existing program and require no human action (like opening a file or running a program) to propagate. Computer worms use recursive methods to copy themselves without host programs and distribute themselves based on exploiting the advantages of exponential growth, thus controlling and infecting more and more computers in a short time. Worms almost always cause at least some harm to the network even if only by consuming bandwidth, whereas viruses almost always corrupt or modify files on a targeted computer.
Destructive potential:
- Worms can cause significant damage by consuming bandwidth, causing systems to become unresponsive, or by delivering a malicious payload that can lead to data loss, unauthorized access, or other forms of damage
Example:
Morris worm:
- One of the first worms distributed via the Internet
- It exploited vulnerabilities in the Unix OS through sendmail, finger, rsh/rexec services and weak passwords.
- The worm’s rapid replication caused DoS on approximately 10% of the 60,000 computers on the ARPANET at the time.
Code Red worm:
- Targeted systems running vulnerable versions of Microsoft’s Internet Information Services (IIS) web server software.
- It propagated by randomly selecting IP addresses to infect, rapidly increasing its spread. Each infected host would then seek out new targets, amplifying its impact.
- The worm defaced websites by replacing their content with a specific message and attempted to launch a denial-of-service attack against the White House’s web server by targeting its IP address.
Trojan Horse
Trojans disguise themselves as legitimate software to deceive users into installing them. Once installed, they perform undesired and harmful actions without user’s knowledge. The name Trojan draws frame the ancient Greek story where soldiers hid inside a wooden horse to infiltrate Troy, similarly, Trojan software hides its malicious functions under the guise of something benign or useful.
- Malicious payload: Once activated, Trojans can carry out a range of destructive actions, from stealing data to damaging the system or even creating a backdoor for attackers to gain remote access
- Unlike worms and viruses, Trojans do not replicate themselves or infect other files. Their spread relies on social engineering tactics to trick users into executing them.
Examples:
- Xbox Games Trojan: This Trojan misled users by claiming to enable Xbox games to run on PC. Instead of delivering on its promise, it modified the Windows Registry to automatically open a specific webpage at boot, generating ad revenue for the creators through increased page views.
- Rogue antivirus: This type of Trojan masquerades as legitimate antivirus software, alarming users with false positives and security warnings. It then coerces them into paying for a fake “update” or “premium protection” that does nothing more than deactivate the Trojan, or worse, it may steal personal and financial information.
Logic Bombs
Logic bombs are malicious code objects that infect a system and lie dormant until they are triggered by the occurrence of one or more conditions such as time, program launch, website logon, and so on.
- Michelangelo virus: It infected a system’s MBR through the sharing of infected floppy disks and then hid itself until March 6—the birthday of the famous Italian artist Michelangelo Buonarroti.
Botnet
Botnet a number of Internet-connected devices, each of which is running one or more bots. – Botnets can be used to perform Distributed Denial-of-Service attacks, steal data, send spam, and allows the attacker to access the device and its connection.
- Mirai Botnet
- Prometei - a new cryptocurrency mining botnet
- Uses varied techniques to spread and compromise systems and stealthily mine Monero (XMR)
- Fritzfrog malware - a P2P Botnet
Spyware and adware
Spyware monitors your actions and transmits important details to a remote system that spies on your activity. For example, spyware might wait for you to log into a banking website and then transmit your username and password to the creator of the spyware. – Alternatively, it might wait for you to enter your credit card number on an ecommerce site and transmit it to a fraudster to resell on the black market.
Adware uses a variety of techniques to display advertisements on infected computers. The simplest forms of adware display pop-up ads on your screen while you surf the web. – More nefarious versions may monitor your shopping behavior and redirect you to competitor websites.
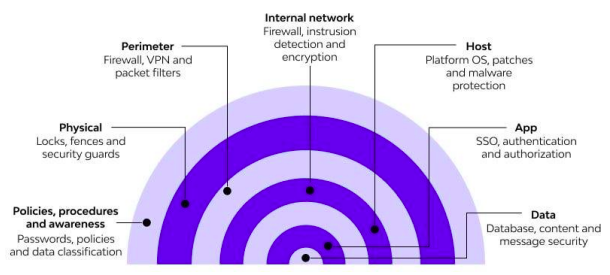
Ransomware
encrypts data on infected systems and demand ransom for decryption keys. The financial damages from ransomware attacks have been soaring, with costs reaching 10 billion in 2019. The evolution of ransomware involves more sophisticated attack vendors and exploitation techniques, indicating that cyber-criminals are continuously enhancing their methods to penetrate systems more effectively and elude detection.
- Initial Access: Attackers gain entry into a victim’s network through various means, including malicious attachments, drive-by downloads, and exploiting vulnerabilities.
- Data Encryption and Ransom Demand: Following entry, attackers delete all shadow copies of data and encrypt the data, then demand a ransom for the decryption key.
Steps:
- The attacker generates a key pair and embeds the victim’s public key into the malware.
- The malware encrypts the victim’s data using a random symmetric key. It encrypts the symmetric key with the victim’s public key, creating asymmetric and symmetric ciphertexts. The malware demands ransom from the victim, providing instructions and the asymmetric ciphertext.
- The victim sends the ransom payment and asymmetric ciphertext to the attacker. The attacker decrypts the asymmetric ciphertext with their private key, obtaining the symmetric key. The attacker sends the symmetric key to the victim, who uses it to decrypt their data, completing the attack.
Evolving extortion strategies:
- Double Extortion: In addition to encrypting data, attackers ex-filtrate sensitive information before encryption and threaten to leak it unless the ransom is paid.
- Triple Extortion: Adds the threat of launching a Distributed Denial of Service (DDoS) attack against the victim’s organization to the double extortion tactic.
- Quadruple Extortion: Further pressures the organization by contacting its users and customers, increasing the likelihood of paying the ransom to avoid reputational damage.
Best practices:
- Data backup: Implement a routine backup schedule and strengthen backup infrastructure to ensure data recovery in case of ransomware attack
- Patch management: Keep software and systems up-to-date by applying patches promptly to address vulnerabilities and reduce risk of exploitation.
- Risk Assessments and Penetration Testing: Conduct regular risk assessments and penetration testing to identify and address potential security weaknesses.
- Least privilege principles: Limit user access rights to the minimum necessary for performing their job functions to reduce the impact of potential security breaches.
- Incident response planning: Develop and test an incident response plan to effectively respond to security incidents, including ransomware attacks.
- Defense in depth: Employ multiple layers of defense mechanisms and invest in innovative security solutions, such as Breach and Attack Simulations (BAS) and AI-powered tools.
- Email filtering: Block file attachments commonly associated with malware and filter out emails with known malicious indicators at the email gateway and firewall.
- Network segmentation: Segregate networks based on tasks or departments to minimize the impact of ransomware attacks and data loss.
Ex: WannaCry began spreading across the globe in May, exploiting a vulnerability in Microsoft OS. WannaCry encrypted data on infected machines, demanding ransom payments in the cryptocurrency Bitcoin in exchange for decrypting the data.
Rootkits
are malicious software designed to give unauthorized access to a computer or other software. Rootkits are hard to detect and can conceal their presence within an infected system. Hackers use rootkit malware to remotely access your computer, manipulate it, and steal data.
Ex: Lojax is a UEFI (Unified Extensible Firmware Interface) rootkit used by APT28 to persist remote access software on targeted systems.
Social Engineering Attacks
represents a significant threat vector in cybersecurity, leveraging human psychology rather than technical hacking techniques to gain unauthorized access to information or systems. It exploits the natural tendency of people to trust, making it highly effective method for attackers to breach security defenses.
Types:
- Basic social engineering: involves direct interaction with the target, such as phone calls where the attacker poses as a trustworthy entity
- Phishing: utilizes deceptive mails or messages that mimic legitimate sources to trick individuals into revealing personal data, clicking on malicious links, or downloading infected attachments.
- Spear phishing: A more targeted form of phishing that involves personalized attacks against specific individuals, using gathered information to make the attack more credible.
- Whaling: Targets high-profile individuals within an organization, like executives, with spear-phishing tactics to gain access to valuable information.
- Vishing (Voice Phishing): Uses phone calls instead of emails to trick individuals into disclosing sensitive information.
- Dumpster Diving: Involves searching through a target’s garbage to find sensitive documents that can be used in further attacks.
- Quishing (QR Code Phishing): Uses QR codes to direct victims to malicious websites or trick them into downloading malware.
Countermeasures;
- Builiding a secure culture
- Endpoint security
- Email and network security
- Penetration testing and simulations
- Phishing-resistant MFA (Multi-factor authentication) (PIV/FIDO2 passkey)
- Continuous monitoring
DoS and DDoS
DoS attacks can result in system crashes, system reboots, data corruption, blockage of services, and more. Another form of DoS attack is a DDoS attack.
- A DDoS attack occurs when multiple systems attack a single system at the same time. For example, a group of attackers could launch coordinates attacks against a single system
- A distributed reflective denial-of-service (DRDoS) attack is a variant of a DoS. It uses a reflected approach to an attack.
- It doesn’t attack the victim directly, but instead manipulates traffic or a network service so that the attacks are reflected back to the victim from other sources.
- Domain Name System (DNS) poisoning attacks and smurf attacks are examples.
Example:
Ping flood attack:
- This is a more straightforward attack where the attacker sends a large number of ping requests directly to the victim’s IP address. This can be done from a single system or, more commonly, from multiple systems in a botnet, turning it into a DDoS attack.
- The victim’s system tries to respond to each ping request with a reply, but the sheer volume of requests can overwhelm the system’s resources, leading to slowed down responses or total unavailability to legitimate traffic.
Smurf attack:
- exploits the ICMP, which is used by the ping command to test the connectivity between systems. In this attack, the perpetrator sends ICMP echo requests packets (ping requests) to a network’s broadcast address, making it appear as though the requests are coming from the victim’s IP address.
- Every host on the network receives this broadcast and responds with an echo reply to the victim’s IP address, thereby flooding the victim with a massive amount of traffic.
Fraggle attack:
- Similar in concept to the Smurf attack, a Fraggle attack uses UDP packets instead of ICMP. It targets UDP ports 7 (Echo) and 19 (Chargen) with packets that have a spoofed source IP address—again, the victim’s address. These packets are broadcast to all systems on a network.
- As with the Smurf attack, the targeted systems respond to the spoofed IP address, creating a flood of traffic to the victim. The use of UDP, a connectionless protocol, makes it easier to generate large amounts of traffic with minimal effort from the attacker.
Defense strategies:
- ingress filters
- rate limiting
- network configuration
- Intrusion Detection Systems (IDS)
- Knowledge-based detection: relies on a database of known attack signatures of patterns
- Behavior-based detection: learns what normal network or system behavior looks like and then monitor for deviations from this baseline
Man-In-The-Middle
is a cyber threat where an attacker secretly relays and possibly alters the communication between two parties who believe they are directly communicating with each other. This attack can be used to steal personal information, such as login credentials and credit card numbers, making it especially dangerous for users of financial applications, e-commerce sites, and other secure web services. The attacker’s aim can range from financial gain to facilitating further attacks, such as Advanced Persistent Threats (APTs).
Phases of a MITM attack: Generally consist of two main phases:
-
Interception: This phase involves capturing the victim’s traffic to redirect it through the attacker’s network.
- IP Spoofing: The attacker deceives the network into thinking their device has the IP address of the victim or another trusted entity, causing the network to send the victim’s data to the attacker instead.
- ARP Spoofing: By sending falsified ARP (Address Resolution Protocol) messages onto the network, the attacker links their MAC address with the IP address of the victim, intercepting messages meant for the victim.
- DNS Spoofing (DNS cache poisoning): This involves corrupting the DNS server to redirect the traffic from a legitimate site to a fraudulent one controlled by the attacker.
-
Decryption: After successfully intercepting the traffic, the attacker must decrypt any secure communications to access the information being exchanged.
- HTTPS Spoofing: deceive the victim’s browser by presenting a fake certificate for a trusted site
- SSL BEAST: attack targets a vulnerability in TLS and older SSL protocols
- SSL Hijacking: intercepts the TCP handshake process between the user and the application. They forge authentication keys, misleading both the user and the application into believing they are communicating securely, while the attacker controls the session and can access transferred data.
- SSL Striping: involves downgrading a secure HTTPS connection to an unencrypted HTTP connection. The attacker intercepts the TLS authentication attempt, serving the user an unencrypted version of the site, while maintaining an encrypted session with the application.
Mitigations:
- Use HTTPS
- Secure DNS
- Public Key Infrastructure (PKI) and Digital Certificates
- VPN Services
- Network Security
- Educate Users
Masquerading Attacks
(more general)
Masquerading attacks involve an attacker presenting themselves as a legitimate entity to deceive users, systems, or both, into granting access to sensitive data or secure systems. These attacks can occur in various forms, including but not limited to, email spoofing, website cloning, and impersonating network entities.
Email spoofing:
- Attackers forge sender addresses in emails to appear as if they are coming from a trusted source, tricking recipients into divulging sensitive information.
- Technical detail: This can be achieved by manipulating the
SMTPheaders, specifically theFrom:field, to display a trusted email address. - Defense: Implement DMARC (Domain-based Message Authentication, Reporting, and Conformance) to authenticate email senders and reduce email spoofing.
Domain Spoofing:
- Similar to email spoofing, attackers register domain names closely resembling legitimate ones, using tactics like typosquatting or IDN homograph attacks, to deceive users.
- Technical detail: Through the use of Punycode, attackers can register domains that visually resemble legitimate ones by exploiting characters from non-Latin scripts that look similar to Latin letters.
- Use DNSSEC (Domain Name System Security Extensions) to protect against domain spoofing by ensuring DNS responses are authenticated.
ARP Spoofing:
- Attackers send fake ARP (Address Resolution Protocol) messages over a local area network to link their MAC address with the IP address of a legitimate host or server, intercepting data meant for that host.
- Technical detail: By continuously sending ARP responses (not requests) to a target’s gateway with the attacker’s MAC address, the attacker can deceive the gateway into sending traffic meant for the legitimate host to the attacker instead.
- Defense: Utilize static ARP entries where feasible, although this may not be scalable for larger networks.
IP Spoofing:
- Here, an attacker sends packets from a forged IP address to disguise their actual location or impersonate another system within a network, often used in Denial-of-Service (DoS) attacks.
- Technical detail: Manipulation of the IP header in network packets allows the attacker to set the source IP address to that of a trusted or internal network device, thus bypassing IP-based authentication and filtering mechanisms.
- Defense: Implement ingress and egress filtering to check that incoming and outgoing packets have valid source and destination IP addresses, respectively.

Session hijacking
…
Password Attacks - Brute Force
Brute force attacks are a class of cyber attack where adversaries attempt to gain unauthorized access to accounts by systematically guessing passwords. These attacks leverage the fact that many users choose weak, common passwords or reuse passwords across multiple accounts.
Password guessing:
This technique involves guessing the passwords of specific accounts without prior knowledge of legitimate credentials. Attackers might use common passwords or variations based on user information (like names, birthdates, etc.) May lead to account lockouts or trigger security alerts due to multiple failed authentication attempts.
Password spraying:
Password spraying reverses the traditional brute force approach by using a small number of common passwords (often from lists of widely used or default passwords) against a large number of accounts. Reduces the risk of triggering account lockouts or alarms, as only a few attempts are made against each account.
Credential stuffing:
This technique uses previously breached or leaked credentials to attempt access on different systems, exploiting users who reuse passwords across multiple accounts. Relies on the large volume of user credentials from past data breaches available on dark web marketplaces or through other means.
Defenses:
- Multi Factor Authentication (MFA)
- Account lockout policies
- Password policies
- User education
- Credential monitoring and awareness
Types of authentication:
Authentication factors are categorized based on the type of evidence they require from users to verify their identity. These categories help in understanding the multifaceted approach to secure authentication.
-
Knowledge factors: Something the user knows
- Passwords
- PINs
- Security questions
-
Possession factors: Something the user has
- Security tokens
- Smart cards
- Mobile phone SMS
-
Inherence factors: Something the user is (biometric factors)
- Fingerprint scans
- Facial recognitition
- Iris scans
-
Location factors: Somewhere the user is (geographical factors)
- Geofencing
- IP address location
-
Behavior factors: Something the user does (behavioral biometrics)
- Keystroke dynamics
- Mouse movements
- Voice recognition
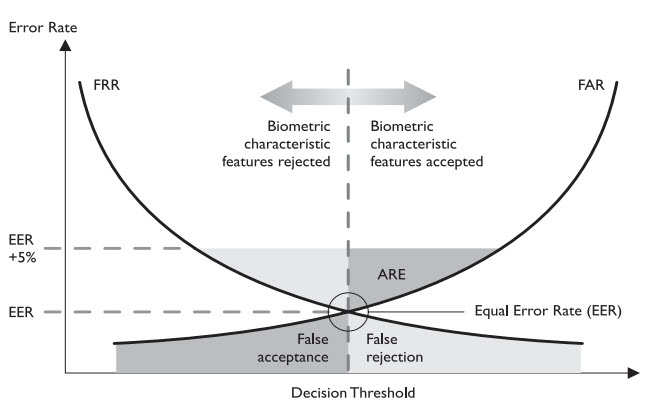
Authentication errors:
Type 1 Error (False rejection rate or FRR): Type 1 error, also known as a False Rejection Rate (FRR), occurs when a biometric system incorrectly rejects an authentication attempt by an authorized user. A fingerprint recognition system fails to authenticate a registered user because of a minor injury to the finger or slight variations in the placement or pressure.
Type 2 Error (False acceptance rate or FAR): Type 2 error, also known as a False Acceptance Rate (FAR), occurs when a biometric system incorrectly accepts an unauthorized individual as a legitimate user. A facial recognition system incorrectly grants access to an individual who resembles a registered user closely enough to deceive the system.
Crossover error rate (CER):
The Crossover Error Rate (CER) is a critical metric in biometric authentication systems. It represents the point at which the rates of False Acceptances (Type 2 errors) and False Rejections (Type 1 errors) are equal. In other words, it’s the rate at which both acceptance and rejection errors occur at the same frequency.
CER is used as a standard measure of a biometric system’s accuracy. A lower CER indicates a more accurate system. This metric is particularly useful for comparing the performance of different biometric solutions, as it provides a single figure that reflects both types of errors.
When choosing among biometric solutions, the CER is a vital consideration. A system with a lower CER is generally more reliable and secure, making it a better choice for applications where accuracy is critical. However, the selection also depends on other factors like the application context, user experience, scalability, and cost. For instance, a system with a slightly higher CER might still be chosen over another if it significantly improves user throughput or reduces costs, assuming the slight increase in error rate is acceptable for the specific use case.
Multi Factor Authentication:
Multi-Factor Authentication (MFA) is a security mechanism that requires users to provide two or more verification factors to gain access to a resource, such as an application, online account, or a VPN.
Phishing-resistant Multi-Factor Authentication (MFA) methods are designed to safeguard against phishing attacks, one of the most common and effective tactics used by attackers to compromise authentication processes. These methods add layers of security that are not susceptible to being stolen or replicated through phishing attempts.
-
FIDO2/WebAuthn: The Fast Identity Online (FIDO) Alliance’s FIDO2 standards, including WebAuthn (Web Authentication), provide a framework for secure and phishing-resistant authentication. These standards allow users to use local authenticators, such as biometrics (fingerprint and facial recognition) or hardware security keys, to authenticate to online services in a way that doesn’t require a password. The authentication process is tied to the original website’s URL, making it immune to phishing attempts as the credentials cannot be reused on a different site.
-
Hardware Security Keys (e.g. YubiKey): Hardware security keys are physical devices that support protocols like U2F (Universal 2nd Factor) or FIDO2 and are used to authenticate a user by being inserted into a USB port or using NFC or Bluetooth.
-
Smart Cards: Smart cards are physical cards embedded with a chip that the user inserts into a reader to gain access. They can store a user’s credentials and perform cryptographic operations.
-
Biometric Authentication: Uses unique biological characteristics, such as fingerprints, facial recognition, or iris scans, for authentication.
-
Behavioral Biometrics: This method analyzes patterns in human activity (e.g., typing behavior, mouse movements) to authenticate users.
-
OTP Tokens: Generates a temporary passcode, typically every 30-60 seconds, used alongside or in place of a password.
Application Attacks
Buffer overflow vulnerabilities exist when a developer does not properly validate user input to ensure it is of an appropriate size. Input that is too large can overflow a data structure to affect other data stored in the computer’s memory.
The time of check to time of use issue is a timing vulnerability that occurs when a program checks access permissions too far in advance of a resource request. Also known as race condition.
Backdoors are undocumented command sequences that allow individuals with knowledge of the back door to bypass normal access restrictions. They are often used during the development and debugging process to speed up the workflow and avoid forcing developers to continuously authenticate to the system.
Once attackers gain a foothold on a system, they often quickly move on to a second objective expanding their access from the normal use account they may have compromised to more comprehensive, administrative access. They do this by engaging in escalation-of-privilege attacks. One of the most common ways that attackers wage escalation-of-privilege attacks is through the use of rootkits.
Buffer overflow:
A buffer overflow occurs when data exceeds the memory buffer’s boundary, overwriting adjacent memory locations. This can lead to arbitrary code execution, crashes, and other types of undefined behavior. Buffer overflows are critical vulnerabilities often exploited in software to compromise systems. They are especially prevalent in languages that do not automatically manage memory, such as C and C++.
- Memory Allocation: In programming languages like C, when data is read into a buffer (a continuous block of memory), the program must manage the memory and explicitly check the amount of data.
- Overflow Condition: If the program does not check or incorrectly checks the length of the data, it can write beyond the allocated space.
- Overwriting Memory: This can corrupt the data in adjacent memory spaces, which might include important control information, such as the return address of a function.
- Exploitation: An attacker can craft input data that, when processed by the vulnerable program, overwrites specific memory locations with payload code (often shellcode) that is then executed by the application
void vulnerableFunction(char *str) {
char buffer[100];
strcpy(buffer, str);
}Defense: bounds checking, safe functions, stack canaries, non executable stack
Web Application Attacks
Cross-site scripting (XSS):
XSS attacks involving injecting malicious scripts into content that is then served to a user’s browser. This vulnerability exploits the trust a user has for a particular site, allowing the attacker to send scripts that the site then unwittingly broadcasts to other users. These scripts run in the context of the user’s browser, appearing as if the trusted site generated them. These scripts execute within the context of the user’s session, allowing attackers to steal cookies, session tokens, or other sensitive information. XSS is classified into three main types:
-
Non-persistent (Reflected): The malicious script is reflected off the web server, such as in an error message or search result. It typically requires tricking the user into clicking a malicious link.
-
Persistent (Stored): The malicious script is permanently stored on the target server (e.g., in a database, message forum, visitor log, or comment field), and when the server serves the stored information to users, the malicious script is served as part of the web page.
-
DOM-based: This form of XSS occurs when the vulnerability exists in client-side code rather than server-side code. This type occurs entirely in the client’s browser without needing to send the malicious script to the server. It manipulates the DOM of the page, causing the client’s browser to execute the script.
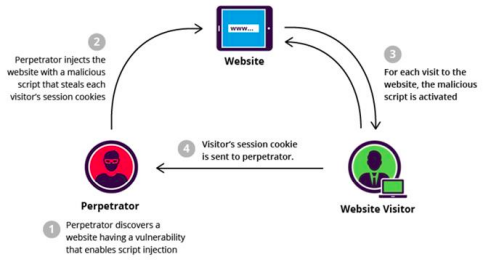
Example: Consider a simple example where a website allows users to post comments that are not properly sanitized for HTML tags or JavaScript content. An attacker could submit a comment that includes a malicious script, such as:
<script> alert('XSS'); </script?
Protection:
- Encode or escape user input before rendering it on the page, especially in places where HTML, URL, Javascript or CSS content is expected
- Use Content Security Policy (CSP) to reduce the severity of an XSS
- Encode data returned to the user to ensure that it is treated as data, not executable code.
- Validate or sanitize user inputs to ensure they conform to expected values
- Employ frameworks and libraries that automatically handle some aspects of XSS prevention. For example, React automatically escapes content before rendering it, significantly reducing the risk of XSS.
Cross-site request forgery attacks:
XSRF is a cyber attack that forces an end user to execute unwanted actions on a web application in which they’re currently authenticated. CSRF attacks specifically target state-changing requests, not theft of data, since the attacker has no way to see the response to the forged request. The vulnerability exists because web applications allow requests to be processed without verifying the user’s intention, relying solely on the user’s authentication cookie or session token.
- User authentication: The victim logs into a web application (e.g. a banking website), which authenticates the user and issues a cookie for session management
- Crafting malicious request: The attacker creates a malicious web page or email that includes a request to the targeted application (e.g. a request to transfer money from the victim’s bank account to the attacker’s account)
- Triggering the request: If the victim visits the attacker’s website or clicks a link in the email while still logged into the target application, the browser automatically includes the victim’s cookies for that site in the request.
- Unintended request execution: The web application fails to distinguish this malicious request from a legitimate one made by the victim, executing the action without the victim’s consent.
a user is logged into bank, the hacker makes user send a form using the same cookie, bank verifies
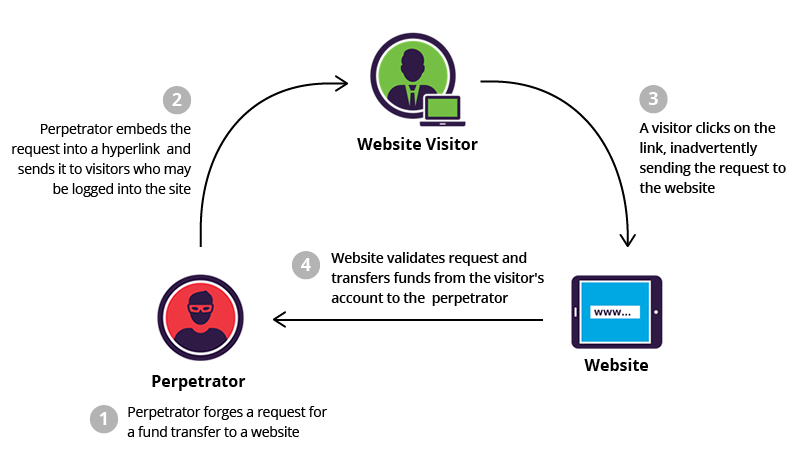
Example:
Imagine a user is logged into their online banking account. The attacker sends the user an email containing an image tag with the src attribute set to an URL that performs a fund transfer on the banking application:
<img src="https://bank.com/transfer?amount=1000&to=attacker" style="display:none;">
When the email is opened, the user’s browser tries to load the image, inadvertently sending a request to the bank’s transfer endpoint with the user’s session cookie. If the bank does not properly verify the request’s origin, it may process the transfer.
Protection:
-
Samesite cookie attribute: Many browsers support the
SameSitecookie attribute, which can prevent the browser from sending cookies with cross-site requests. -
Referer validation: Checking the
Refererheader of incoming requests can help ensure that the request originated from the application’s own domain. However, this method is less reliable due to users or proxies that strip theRefererheader for privacy reasons -
Anti CSRF tokens: A server can generate a unique token for each session or for each transaction. This token must be included in every state-changing request by the client. Since an attacker cannot obtain this token, they cannot forge a valid request.
-
Double submit cookie: The server sets a cookie with a unique value for each session, and the client must submit this value as a hidden form field or in a custom HTTP header with each request. The server then compares the cookie value to the form or header value, ensuring they match.
-
Content security policy (CSP): Implementing CSP can prevent the execution of unauthorized scripts, reducing the risk of CSRF as part of a broader XSS mitigation strategy.
SQL injections:
SQL injections exploits vulnerabilities in web applications by injecting malicious SQL code into queries. This can lead to unauthorized access to or manipulation of database information. The vulnerability is present when user input is either incorrectly filtered for string literal escape characters embedded in SQL statements or user input is not strongly typed and unexpectedly executed.
Types:
-
In-band SQLi: The attacker uses the same communication channel to launch the attack and gather results. This method is straightforward because it involves directly receiving the outcome of the malicious SQL queries through the application’s responses.
- Error-based: gathering and collecting SQL error messages that contain info about database structure
- Union-based: exploits the union sql operation, allows combination of two or more select statements into a single result set
-
Blind SQLi: Blind SQLi (Inferential SQLi) occurs when the attacker cannot directly see the data resulting from an attack because the application does not display data about the injection result.
- Boolean-based blind: forces application to return a different result depending on whether the query is true or false
- Time-based blind: attacker crafts a sql query that causes the database to wait for a specified amount of time
-
Out of band SQLi: an attacker is unable to use the same channel for the attack and the data retrieval, so via DNS looups or HTTP requests
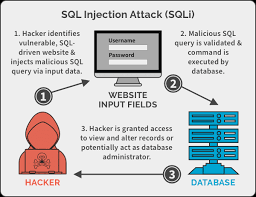
Example:
User enters - username:Alice and password:password123. Your website sends this query to the database:
SELECT * FROM users WHERE username = 'Alice' AND password = 'password123';
If the username and password match what’s in the database. Alice gets logged in.
Attacker enters - username:’ OR 1=1
SELECT * FROM users WHERE username = '' OR '1'='1' AND password = '...';
Protection:
- Use prepared statements with parameterized queries
- Employ stored procedures
- Implement ORM libraries
- Validate input data
- Use web application firewalls
- Regularly update and patch
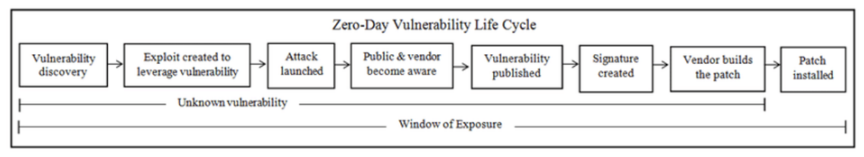
Zero Day
A zero-day vulnerability refers to a flaw in software that is unknown to the software maker or has no patch available at the time it becomes known to others. These vulnerabilities are highly prized by attackers because they can be exploited to carry out various malicious activities before a fix is developed and distributed.
Exchange Server Zero-Day Vulnerability Incident:
- Microsoft released an out-of-band emergency security update on March 2021 to address four actively exploited vulnerabilities. The vulnerabilities affected Microsoft Exchange Server 2015, 2016 and 2019
- The exploitation was attributed to cyber-espionage groups of Chinese origin, including LuckyMouse, Tick Calypso.
- Attackers deployed web shells, such as China Chopper, on compromised servers
- Further operations by attackers: credential dumping, addition of user accounts, stealing copies of the active directory database
 (some CVE stuff is there)
(some CVE stuff is there)
Examples:
- Stuxnex worm: targeted at Iran’s nuclear facilities exploited several zero-day vulnerabilities in Windows to infiltrate and sabotage zero-day vulnerabilities
- Eternal blue: discovered by NSA in Microsoft’s SMB protocol, used in wannacry
- Pegasus spyware: a series of zero day in iOS to remotely jailbreak iphones and install surveillance software
Reconnaissance Attacks
Reconnaissance attacks involve gathering information about a target to identify vulnerabilities for exploitation:
IP Probes:
- Attacker conducts IP probes (or ping sweeps) to identify active systems on the target network.
- Tools like Nmap are commonly used for IP probes and port scans.
Port Scans:
- After identifying active systems, attackers perform port scans to determine which public services are running on each machine.
- Targeted systems, such as web servers or file servers, are prime targets for exploitation.
Vulnerability Scans:
- Once a specific system is targeted, attackers seek out vulnerabilities that can be exploited to gain access.
- Tools like Nessus, Open
Cyber Threat Modeling and Threat Hunting
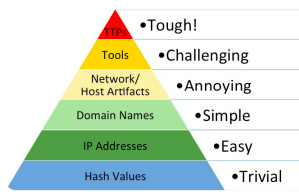
Threat intelligence represents a comprehensive understanding of potential security threats facing an organization, blending insights into the motivations, intentions, and capabilities of both internal and external adversaries.
- This form of intelligence encompasses evidence-based knowledge that includes not only the context and mechanisms of threats but also specific indicators, implications and actionable advice to counter existing or emerging menaces.
- It details the tactics, techniques and procedures (TTPs) utilized by these adversaries, offering a strategic perspective that aids in the formulation of informed business decisions aimed at migrating risks and addressing the implications of these security challenges.
- At its core, threat intelligence serves a proactive role in an organization’s security posture, enabling decision-makers to anticipate potential threats and draft strategic response tailored to the unique threat landscape they face.
- By providing a detailed analysis of the threat actors’ methodologies and objectives, threat intelligence empowers organizations to enhance their defenses, prioritize security investments, and develop effective countermeasures. Through this lens, the ultimate goal of threat intelligence is to fortify organizational assets against potential security breaches and minimize the impact of cyber threats on business operations.
Key components:
- Understanding threat actors
- Tactics, techniques, and procedures
- Evidence-based knowledge
- Context and implications
- Actionable advice
| Type | Purpose | Focus | Usage | Examples |
|---|---|---|---|---|
| Strategic | Provides a comprehensive view of the cyber threat landscape over the long term. | Addresses “who” and “why” questions, such as who the potential attackers are, their motivations, the industries or sectors they target, and their preferred TTPs. | Used by senior leadership to shape cybersecurity policies, strategies, and risk management frameworks. | Reports on APT groups targeting the financial sector, analyses of geopolitical factors influencing cyber espionage campaigns. |
| Tactical | Offers immediate to near-real-time information about specific threats and incidents. | Concentrates on specific indicators of compromise (IOCs) such as malicious IP addresses, domains, file hashes, and phishing email indicators. | Primarily utilized by SOC teams and cybersecurity analysts for real-time alerting and threat detection in tools like SIEM systems. | Feeds containing malicious IP addresses involved in a current attack campaign, signatures of newly discovered malware. |
| Operational | Focuses on the day-to-day management and mitigation of cyber threats with frequently updated information. | Provides insights into emerging threats and vulnerabilities that could impact the organization in the short term, including new attack vectors and mitigation recommendations. | Utilized by network/system administrators and security managers to make informed decisions about security posture adjustments. | Alerts about an emerging DDoS threat leveraging a new vulnerability, advisories to patch specific software vulnerabilities. |
Why use Threat Intelligence?
Strengthen defense: helps organization increase the cybersecurity resilience and strengthen the defenses by pointing out common attack points used by hackers
Uncover the unknowns: help identify areas of the IT landscape that might not have been covered by the already established rules and alerts in place.
Identification of threats: help identify current threats in the IT landscape of the organization and will work as living database of known indicators of compromise
Specified threat hunting: enrich the logs and help identify specific areas of interest for threat hunting in the IT landscape of the organization by creating awareness on potential areas of compromise.
Threat modeling concepts and methodologies
Threat modeling is the security process where potential threats are identified, categorized, and analyzed. Begin threat modeling early in the design process of a system and continue throughout its life-cycle. For example:
- Microsoft uses a SDL process to consider and implement security at each stage of product’s development.
- This supports the motto of Secure by Design, Secure by Default, Secure in Deployment and Communication (also known as SD3+C). It has two goals in mind with this process:
- To reduce the number of security related design and coding defects
- To reduce the severity of any remaining defects
Proactive approach: to threat modeling takes place during the early stages of systems development, specifically during initial design and specifications establishment. This type of threat modeling is also known as a defensive approach. This method is based on predicting threats and designing in specific defenses during the coding and crafting process, rather than relying on post-deployment updates and patches.
A reactive approach to threat modeling takes place after a product has been created and deployed. This type of threat modeling is also known as adversarial approach. This technique of threat modeling is the core concept behind ethical hacking, penetration testing, source code review, and fuzz testing.
Steps of threat modeling:
- Identifying threats
- Determining and diagramming potential attacks
- Performing reduction analysis
- Remediation of threats
Identifying threats
Focus on asset, software, attackers
STRIDE
Microsoft developed a threat categorization scheme known as the STRIDE threat model:
-
Spoofing, involves an attacker impersonating something or someone else to gain unauthorized access to systems, data, or networks.
-
Tampering, refers to the unauthorized modification of data, could happen in transit over a network or in storage
-
Repudiation, involves an attacker performing an illicit operation or transaction in such a way that there is no proof of their actions, denying their involvement.
-
Information disclosure, involves unauthorized access to and disclosure of confidential information.
-
Denial of service, aims at making a resource (server, website, application) unavailable to its intended users, denying them the service provided by the resource.
-
Elevation of privilege, occurs when an attacker gains higher access levels or privileges within a system than what is authorized, often leading to unauthorized access to confidential data or control over system functions.
PASTA
The Process for Attack Simulation and Threat Analysis (PASTA) is a seven-stage threat modeling methodology. PASTA is a risk-centric approach that aims at selecting or developing countermeasures in relation to the value of the assets to be protected. It integrates security considerations into the software development process by focusing on the attacker’s perspective and potential attack vectors. PASTA is designed to be adaptable, catering to the specific needs and risk tolerance of an organization.
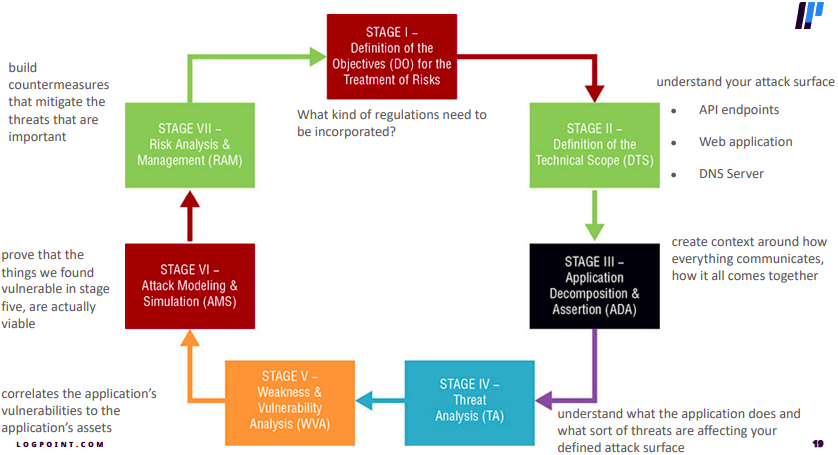
-
Define objectives: focuses on understanding the business context, primary goals, and identifying the key assets
-
Define technical scope: involves delineating technical scope of the application or system, including its architecture, technologies used, and the flow of data
-
Application decomposition: the system is broken down into its constituent components and functionalities
-
Threat analysis: identify potential threats by considering various factors such as motives, capabilities, and methods of potential attackers
-
Vulnerability and weakness analysis: aims to identify existing vulnerabilities within the system that could be exploited by the threats identified in the previous phase
-
Attack modeling: focus shifts to simulating potential attacks based on the identified threats and vulnerabilities.
-
Risk and impact analysis: involves assessing the risk associated with identified threats and vulnerabilities, considering both the likelihood of occurrence and the potential impact on the organization.
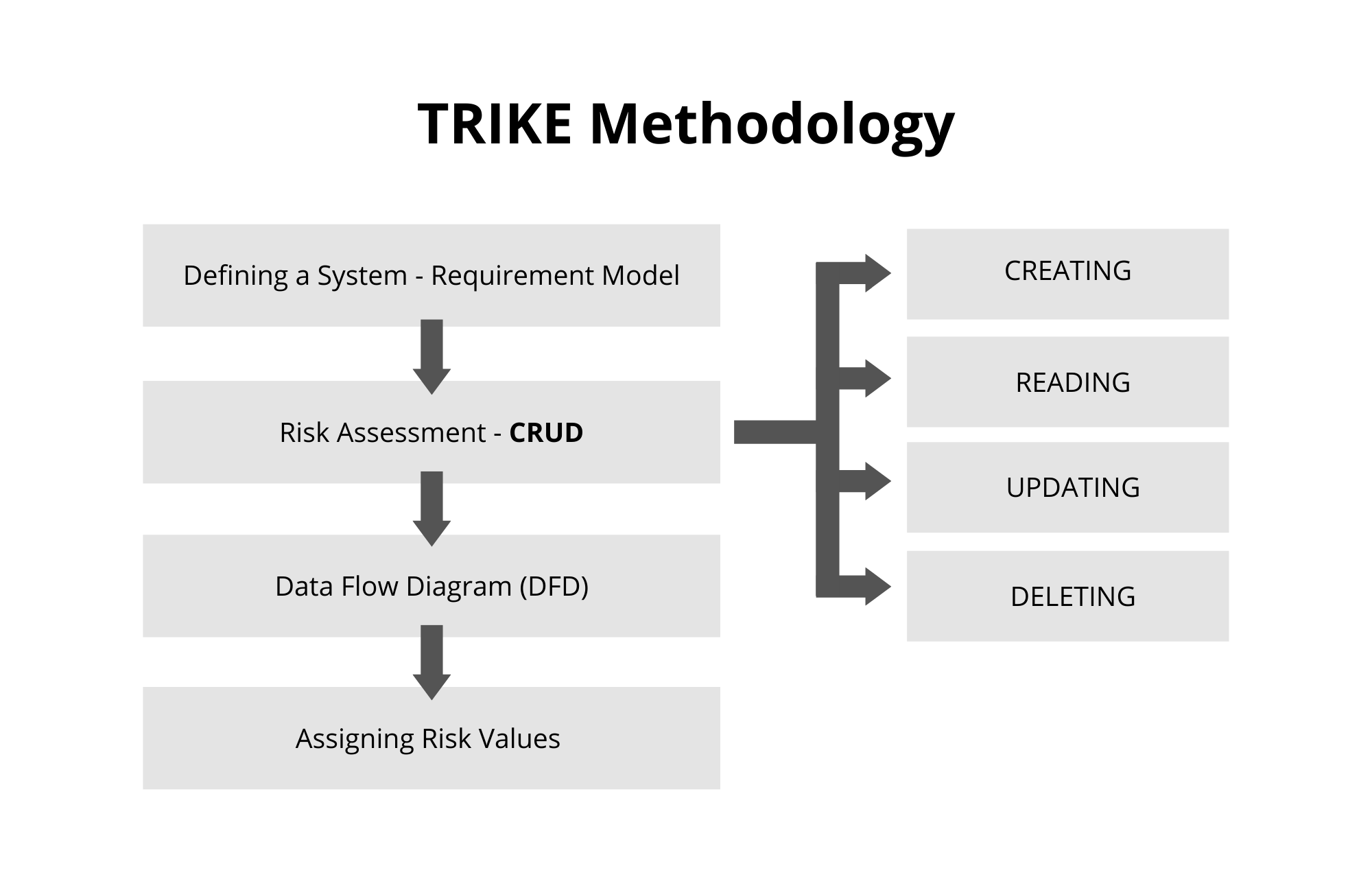
Trike
OCTAVE
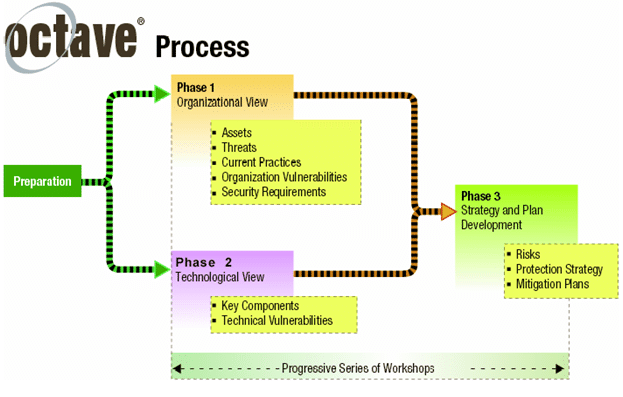
Determining and Diagramming potential attacks
Why DFD bad?
- False Positives, False Negatives and a False Sense of Security in DFDs
- DFD Threat Modeling Is an Incomplete Process
- DFD Boundary Objects Don’t Depict Accurate Threat State
- DFDs Miss Contextual Information of End Point Components
- DFDs Are Time Consuming
- DFDs Miss Threats at Differing Layers of the System
| Aspect | DFDs | PFDs |
|---|---|---|
| Focus | Focus on how data flows through a system from one component to another. | Focus on how a user or attacker progresses through the features/functionality of an application. |
| View of System | Provide a high-level view of the system architecture. | Provide a holistic view of the system architecture and infrastructure. |
| Common Methodology | Commonly used with the STRIDE threat modeling approach. | Used with the VAST (Visual, Agile, Simple Threat modeling) methodology. |
| Threat Generation | Generate threats based on data flows and trust boundaries between components. | Identify threats from an attacker’s perspective and potential attack vectors. |
| Accuracy | Can lead to false positives, false negatives, and incomplete threat coverage. | Avoid false positives by considering upstream/downstream components. |
| Coverage | Lack context about components and miss threats at different system layers. | Cover threats across different layers like web, application, database, etc. |
| Implementation | Time-consuming and require security expertise to create. | Align well with agile development and how developers think about applications. |
| Collaboration | — | Enable collaboration across teams and a self-service threat modeling approach. |
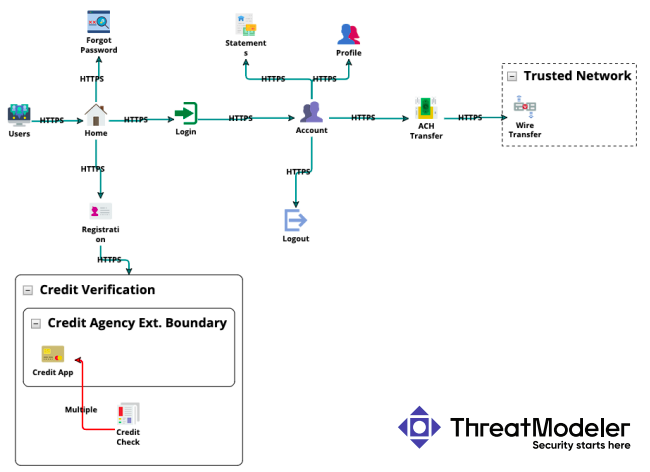
Data Flow Diagram:
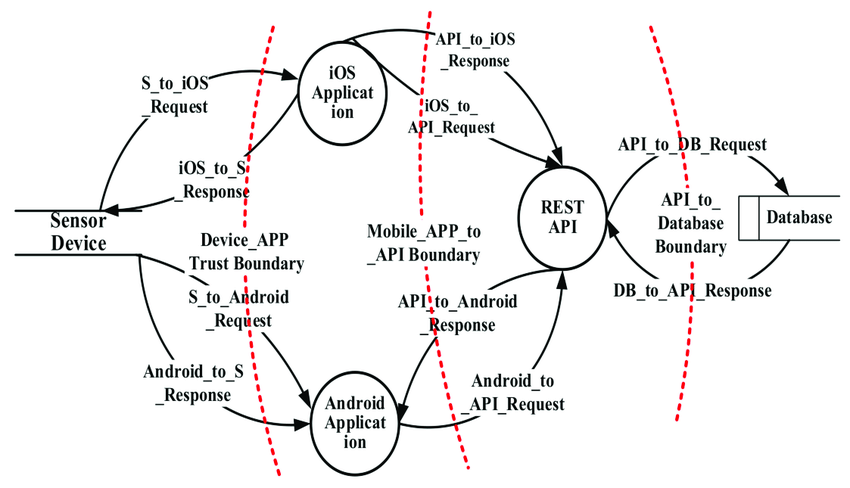
Process Flow Diagram:
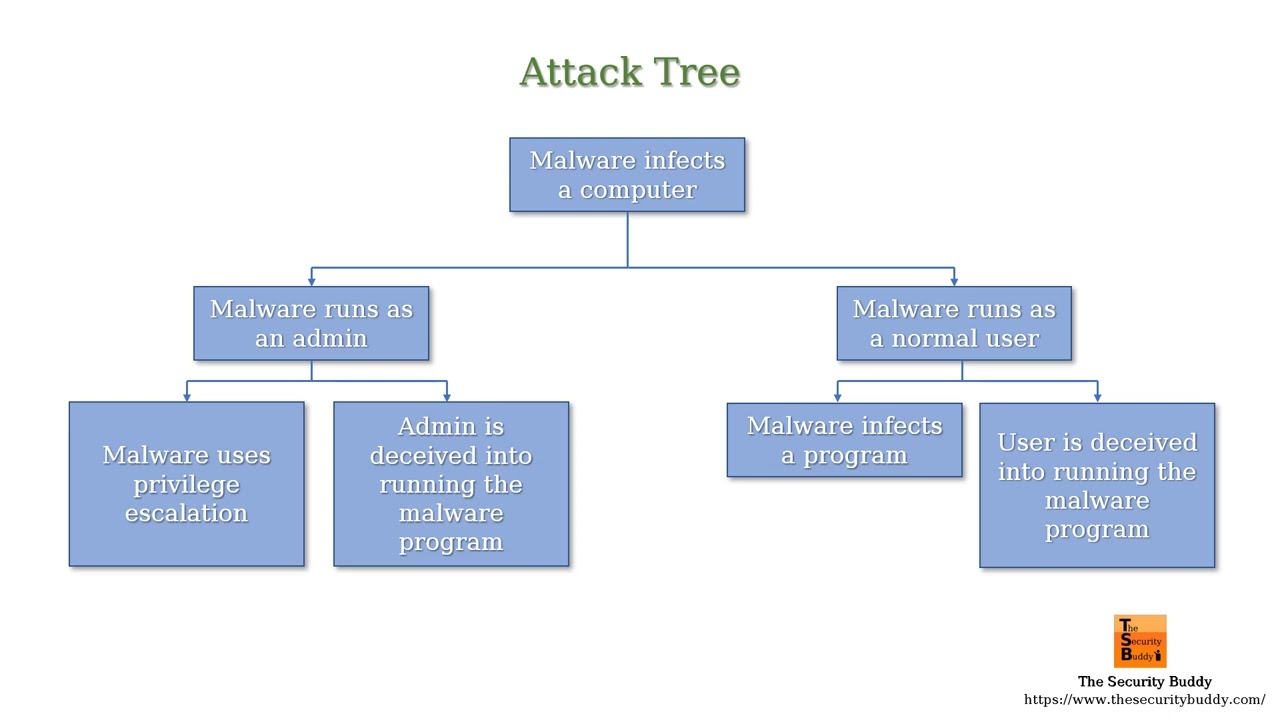
Attack Tree:
Performing reduction analysis
The purpose of this task is to gain a greater understanding of the logic of the product as well as its interactions with external elements. Whether an application, a system, or an entire environment, it needs to be divided into smaller containers or compartments. Those might be subroutines, modules, or objects if you’re focusing on software, computers, or operating systems; they might be protocols if you’re focusing on systems or networks.
In the decomposition process, you must identify five key concepts:
- Trust boundaries: any location where the level of trust or security changes
- Data flow paths: the movement of data between locations
- Input points: locations where external input is received
- Privileged operations: any activity that requires greater privileges than of a standard user account or process, typically required to make system changes or alter security
- Details about security stances and approach: declaration of the security policy, security foundations, and security assumptions
Remediation of threats
As threats are identified through the threat modeling procedure, document it. In this documentation, define the means, target, and consequences of a threat. After documentation, rank or rate the threats. This can be accomplished using a wide range of techniques, such as Probability × Damage Potential ranking, high/medium/low rating, or the DREAD system. The DREAD rating system is designed to provide a flexible rating solution that is based on the answers to five main questions about each threat:
- Damage potential: How severe is the damage likely to be if the threat is realized?
- Reproducibility: How complicated is it for attackers to reproduce the exploit?
- Exploitability: How hard is it to perform the attack?
- Affected users: How many users are likely to be affected by the attack (as a percentage)?
- Discoverability: How hard is it for an attacker to discover the weakness?
Attack Surface Analysis
The attack surface encompasses all the vulnerabilities or weaknesses in an organization’s security controls that attackers could exploit to inflict harm. This includes every potential entry point an attacker might use to gain unauthorized access to confidential data or execute cyberattacks, such as:
- Security gaps in IoT and smart devices
- Vulnerabilities in mobile devices
- Weaknesses in home and corporate networks
- Flaws in data center security
- Vulnerabilities in the supply chain
Objectives:
The ultimate goals of performing an attack surface analysis are to reduce, prevent, and mitigate risks arising from various sources, including IT assets, human error, vulnerabilities in software, targeted attacks, intellectual property infringement, and supply chain risks.
- What: Identifying which parts of the infrastructure are vulnerable and determining the necessary security controls.
- Where: Determining where to apply defense-in-depth protection strategies across the organization.
- When: Understanding when the attack surface changes due to new technologies, policies, or external factors.
- How: Formulating strategies to minimize risks and protect the organization from cyberattacks effectively.
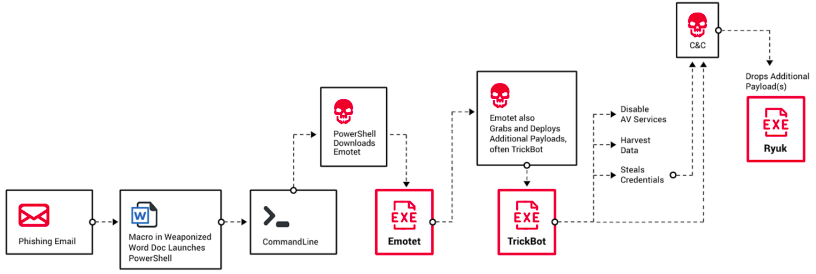
Cyber Kill Chain
is a framework developed by Lockheed Martin to describe the stages of a cyber attack, from early reconnaissance to the final objective achievement. It is derived from a military concept and adapted to cyber security to help organizations understand and respond to cyber threats systematically. The framework outlines a series of phases that an attacker goes through to successfully compromise a system or network.
- Reconnaissance: The attacker gathers information on the target to identify vulnerabilities. This could involve collecting publicly available information, social engineering, or scanning networks for open ports and services.
- Weaponization: Based on the information gathered, the attacker creates a weapon tailored to exploit the vulnerabilities identified. This often involves pairing a remote access malware with a delivery mechanism, like a phishing email.
- Delivery: The weapon is delivered to the target. This could be through emails, malicious websites, USB drives, or other means to ensure the malware reaches the targeted system.
- Exploitation: The delivered malware exploits a vulnerability within the target’s system, allowing the attacker to execute code on the target system.
- Installation: The malware installs a backdoor or other malicious payload on the target system, ensuring persistent access for the attacker.
- Command and Control (C2): The compromised system establishes a connection to an attacker-controlled server, which can be used to remotely control the infected machine and exfiltrate data.
- Actions on Objectives: With the established access, the attacker can now carry out their primary objectives, whether it’s data exfiltration, system disruption, or destruction.
MITRE ATT&CK
The MITRE ATT&CK framework is a comprehensive matrix of tactics and techniques used by threat actors during cyber attacks. Developed by MITRE, a not-for-profit organization that operates research and development centers sponsored by the federal government, ATT&CK stands for Adversarial Tactics, Techniques, and Common Knowledge. The framework is widely used by security professionals to understand adversaries’ behaviors, improve threat detection and response, and develop more effective cybersecurity measures.
Threat Hunting
Threat hunting is a proactive cybersecurity practice where skilled defenders search actively through networks and datasets to detect and isolate advanced threats that evade existing security solutions. Unlike traditional security measures that rely on automated alerts to identify malicious activity, threat hunting involves manual or semi-automated techniques, driven by hypotheses about potential threats. This process allows organizations to identify and mitigate hidden, advanced threats before they can cause significant damage.
- Assume breach principles
- Requires mature organizations
| Hunting Type | Approach | Trigger | Assumption/Methodology | Tools/Frameworks | Example |
|---|---|---|---|---|---|
| Structured | Methodical, based on studying known threat actors and their TTPs. | Knowledge of specific threat actors and their methods. | Threat actors tend to reuse or modify their TTPs over time, which can be detected in network data and logs. | MITRE ATT&CK framework | Searching for traces of an APT group’s known privilege escalation sequence in activity logs. |
| Unstructured | Reactive and triggered by immediate concerns like IOCs. | Detection of an IOC (suspicious file, IP address, domain name) by security tools or user reports. | Investigating the origin, scope, and impact of the IOC to uncover related threats. | Security tools that detect IOCs | Investigating a file with a suspicious hash to trace its origins and behavior on the network. |
| Situational | Investigative, based on hypotheses about the network or specific entities. | Hypotheses or questions about anomalies or security issues within the network. | Uses data analysis to test hypotheses and discover anomalies or patterns indicating a threat. | Data analysis and analytics tools | Analyzing data transfer volumes of an application to identify potential data exfiltration activities. |
Threat hunting methodologies:
Awareness-based hypothesis: draws upon the security team’s situational awareness and existing knowledge about the organization’s IT environment.
Intelligence-based hypothesis: created based on typical TTPs, the hunters observe and inspect the network and systems to ascertain if these TTP behaviors are observed within the environment.
Analytics-driven hypothesis: created based on the use of existing structured frameworks and models, as well as information derived from machine learning and artificial intelligence.
Threat hunting tools:
-
Managed detection and response (MDR): MDR services provide organizations with external expert teams that handle the detection, analysis, investigation, and response to threats. Ideal for organizations lacking in-house cybersecurity resources or expertise, offering an outsourced solution to comprehensive threat management.
- Remote threat hunting and incident response
- Continuous monitoring and analysis of threats
-
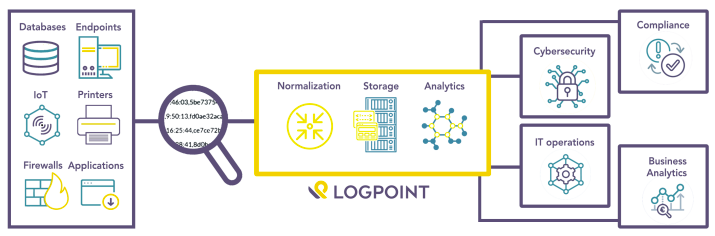
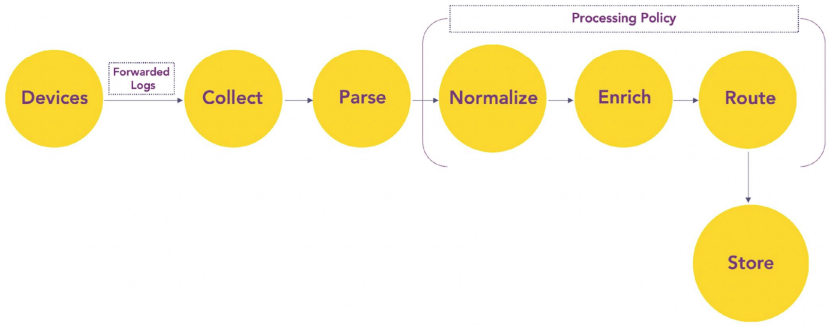
Security Information and Event Management (SIEM): SIEM systems aggregate and analyze security data from various sources within the network to identify anomalies and potential threats. Suitable for organizations requiring a comprehensive overview of their security posture and real-time threat detection and response capabilities.
- Real-time analysis and altering on security events
- Log management and correlation from diverse sources.
-
Security analytics: Security analytics tools apply advanced algorithms and analytical techniques to identify vulnerabilities and potential threats in IT systems. Perfect for organizations looking to deepen their analytical capabilities in threat detection, offering insights into complex data sets.
- Data visualization with graphs and charts for easy interpretation.
- Detection of correlations and patterns indicating threats.
-
Endpoint detection and response (EDR): EDR solutions focus on monitoring endpoint and network events, gathering activity data to identify threat patterns, and responding to detected threats. Essential for organizations aiming to strengthen endpoint security, providing detailed analysis and immediate response to threats detected on endpoints
- Collection of endpoint activity data.
- Automatic threat detection, containment, and response.
- Forensic analysis and investigation.
Log Management
Log management is the practice of continuously gathering, storing, processing, synthesizing and analyzing data from disparate programs and applications in order to optimize system performance, identify technical issues, better manage resources, strengthen security and improve compliance. An effective log management system and strategy enables real-time insights into system health and operations.
An effective log management solution provides organizations with:
- Unified data storage through centralized log aggregation
- Improved security through a reduced attack surface, real-time monitoring and improved detection and response times
- Enhanced customer experience through log data analytics and predictive modeling
- Faster and more precise troubleshooting capabilities through advanced network analytics
Emerging technologies
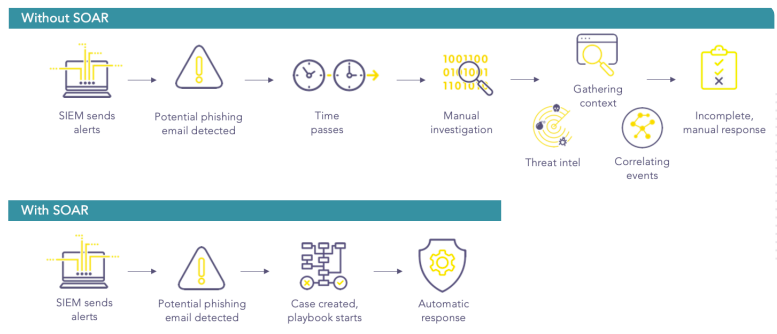
SOAR:
SOAR automatically investigates alert data from SIEM and other security systems and recommends a response. Analysts simply approve or execute that decision, greatly increasing SOC productivity, even with limited resources.
- Security orchestration connects and integrates disparate internal and external tools via built-in custom integrations and application programming interfaces. Connected systems may include vulnerability scanners, endpoint protection products, UEBA firewalls, IDS, IPS systems, security information and event management platforms, endpoint security software, external threat intelligence feeds and other third-party sources.
- The more data gathered through these sources, the better the chance of detecting threats, along with assembling more complete context and improving collaboration. The tradeoffs, however, are more alerts and more data to ingest and analyze. Where security orchestration collects and consolidates data to initiate response functions, security automation takes action.
- Security automation, fed by the data and alerts collected from security orchestration, ingests and analyzes data and creates repeated, automated processes to replace manual processes. Tasks previously performed by analysts, such as vulnerability scanning, log analysis, ticket checking and auditing capabilities, can be standardized and automatically executed by SOAR platforms. Using artificial intelligence (AI) and machine learning to decipher and adapt insights from analysts, SOAR automation can prioritize threats, make recommendations and automate future responses. Alternately, automation can elevate threats if human intervention is needed.
User and entity behavior analysis (UEBA)
represents a sophisticated approach to cybersecurity, leveraging the power of behavioral analytics, machine learning (ML), and automation to detect abnormal activities that could signify security risks. By focusing on both users and devices, UEBA provides a comprehensive tool for identifying potential insider threats, compromised credentials, and other sophisticated attacks that traditional security measures might overlook.
The transition from User Behavior Analytics (UBA) to UEBA marks an evolution in the scope of behavior analysis technologies. Originally focused solely on end-user behaviors, the inclusion of non-user entities in UEBA allows for a broader and more nuanced understanding of potential security threats within a network.
- UEBA is particularly effective at spotting potential insider threats, whether from malicious insiders or external actors using compromised credentials.
- UEBA systems assign risk scores to detected anomalies, helping security teams prioritize their response efforts based on the severity of the threat.
- Low-level alerts are documented and monitored over time. This historical insight can help identify slow-moving, persistent threats that might otherwise go unnoticed.
For example, if a user regularly downloads 5 MB of files each day and then suddenly begins to download gigabytes worth of files, a UEBA solution would identify this user behavior pattern deviation and alert IT of a possible security threat.
Endpoint detection and response (EDR)
Endpoint Detection and Response (EDR) solutions are critical in the cybersecurity landscape for their comprehensive approach to protecting endpoints—devices like computers, mobile devices, and servers—from cyber threats. EDR solutions go beyond traditional antivirus capabilities by incorporating advanced technologies such as machine learning (ML) to offer a robust defense mechanism against sophisticated attacks. EDR solutions are designed to record and store endpoint-system-level behaviors, analyze this data to detect suspicious activity, block malicious actions, and offer remediation guidance to restore affected systems.
Next-Generation EDR solutions enhance traditional antivirus (AV) capabilities by integrating machine learning and EDR features to improve the detection of novel and sophisticated cyber threats. Utilizes ML algorithms to analyze behavior patterns and detect anomalies that may indicate a security incident.
XDR is viewed as an extension of EDR (hence the “X” in XDR), aiming to consolidate data from multiple sources such as email, cloud services, and identity detection systems into a unified platform. XDR extends the capabilities of EDR and Network Detection and Response (NDR) by incorporating additional data sources and security layers, offering a more comprehensive view of threats across the entire IT ecosystem.
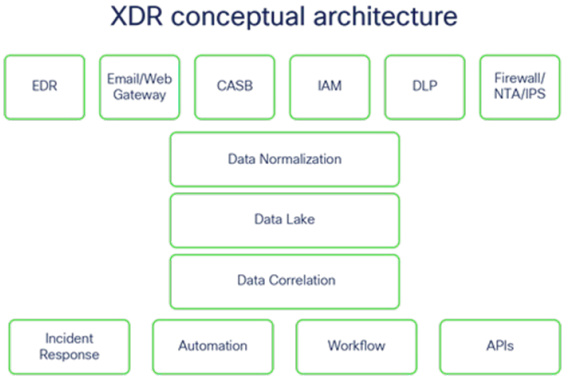
The convergence
- EDR and XDR can feed data to SIEM, which can provide a centralized repository and analysis of the security events and alerts. SIEM can also enrich the data with additional context or intelligence from other sources, such as threat feeds or databases.
- SIEM and SOAR can work together to automate and optimize the security operations and incident response processes. SIEM can trigger SOAR to run predefined workflows or playbooks based on the severity or the type of the alerts. SOAR can also update SIEM with the status or the outcome of the response actions.
- XDR and SOAR can work together to provide cross-platform detection and response capabilities. XDR can leverage SOAR to perform response actions across multiple security tools, such as isolating an endpoint, blocking a network connection, or revoking an identity. SOAR can also leverage XDR to provide visibility and analysis of the threats across multiple vectors.
Quantum cyber security
Quantum computing represents a significant leap forward in computational capability, leveraging the principles of quantum mechanics to process information in ways that traditional binary computing cannot match. However, this powerful technology also poses potential cybersecurity threats, particularly to the cryptographic systems that underpin much of today’s digital security infrastructure.
- Many current encryption methods, such as RSA and ECC (Elliptic Curve Cryptography), rely on the computational difficulty of problems like integer factorization and discrete logarithms for their security. Quantum computers, using algorithms like Shor’s algorithm, could solve these problems much more efficiently than classical computers, potentially rendering these encryption methods vulnerable.
- Digital signatures are vital for verifying the authenticity of digital messages and documents. Quantum computing could compromise the security of digital signatures, affecting everything from secure email to software updates and financial transactions.
- The ability of quantum computers to break current encryption standards could endanger all forms of secure digital communication, exposing sensitive information to unauthorized access.
- Harvest now, decrypt later: Even before quantum computers are widely available, adversaries could collect encrypted data with the intention of decrypting it in the future, once quantum computing technology becomes accessible.
Preparation:
-
Post-quantum cryptography (PQC)
-
Quantum key distribution (QKD): QKD is a method of secure communication that uses quantum properties to secure a communication channel. Unlike traditional methods, the security of QKD does not depend on the hardness of mathematical problems and could offer a way to secure communications against quantum attacks.
Incident Detection and Response
The adage “it’s not a matter of ‘if’ but ‘when’” encapsulates the inevitability of facing a security incident. Recognizing this, preparing for and executing a well-planned response can increase an attackers operational cost and dramatically reduce the business impact of a major cybersecurity incident to your organization.
When a threat becomes a valid attack, it is classified as an information security incident if:
- It is directed against information assets
- It has a realistic chance of success
- It threatens the confidentiality, integrity, or availability of information assets
What is IRP?
The IRP is a detailed set of processes and procedures that anticipate, detect, and mitigate the impact of an unexpected event that might compromise information resources and assets.
Example: NIST Special Publication 61 REV 2
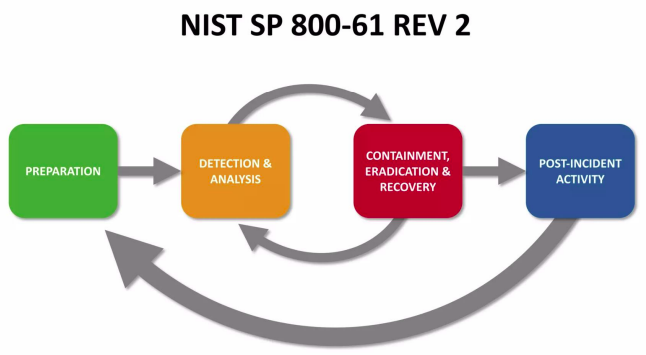 IRP Framework
IRP Framework
-
Preparation:
- incident response plan (team, procedures, docs),
- incident response playbook (phishing, keylogger, ddos)
- logisitcs (meeting, rooms, laptops, storage, printers)
- contacts
- support
-
Detection
- who/what detected/reported threat? time and date? how was reported? similar past threats? is valid?
-
Categorization
- target of threat (user, system, data)
- is this on going/live threat?
- impact of the threat
- categorize the priority of the incident
- classify the incident communication
-
Containment
- coordinate incident management
- isolate the asset
- compromise vectors (ip ports, emails)
-
Investigation
- threat network analysis (firewall, asset logs, traffic data, siem)
- threat malware analysis (footprints, behavior, reverse engineering)
- threat system analysis
- threat user analysis
- threat research analysis
-
Remediation
- network remediation (block ip, domains, emails)
- malware
- system
- user
-
Reporting
- on going reporting
- evidence gathering
- incident documentation
- incident register
- incident report communication
-
Lessons learnt
- root cause analysis
- controls and processes readiness
- incident trends analysis
- mitigation plan
- improvements plan (stop future)
Information Security Policies And Audit
Every organization, regardless of its size or industry, operates within a framework of governance. This governance structure is essential for ensuring that all actions and activities within the organization align with internal policies, as well as external legal and regulatory requirements.
Policies:
An effective Information Security (InfoSec) program is fundamentally anchored in well-crafted policies. These policies, issued by an organization’s management, sever as the cornerstone for security information and information assets, guiding the behavior and actions of employees and other individuals within the workplace.
Key aspects:
- Guidance for proper behavior
- Structure and organization
- Management’s will
- Productive work environment
- Risk management
- Compliance and legal requirements
Policies are important reference documents for internal audits and for the resolution of legal disputes about management’s due care and diligence, and policy can act as a clear statement of management’s intent.
For example:
- Acceptable use policy
- Data breach response policy
- Disaster recovery plan
- Business continuity plan
- Remote access policy
- Access control policy
Characteristics of a good security policy:
- Concise and clear
- Understandable
- Procedurally tolerable
- Usable
- Realistic
- Legal compliance
- Economically feasible
- Consistent
- Based on standards and regulations
Need for security policy:
- Provide consistent application of security protocols throughout the organization
- Ensure information security standards compliance
- Limit the organization’s exposure to external information threats
- Quick respond to security incidents
Policies are the least expensive means of control and often the most difficult to implement.
- The costs associated with policies primarily involve the time and effort required for the management team to develop, approve, and communicate them, as well as the time and effort for employees to integrate the policies into their daily activities.
- Even if the management team seeks assistance from outside consultants to develop policies, the costs remain relatively minimal compared to implementing other forms of control, particularly technical controls.
- Factors such as impracticability, lack of commitment from employees, and misalignment with organizational objectives can hinder successful policy implementation.
Whats in a fucking acceptable policy?
- Purpose
- Scope
- Responsibilities (acceptable use and unacceptable use)
- Monitoring
- Security and confidentiality
- Breaches, investigations and discipline
- Others: contact information, where to find more info, glossary
Standards:
Standards define compulsory requirements for the use of hardware, software, technology, and security controls. Mandatory activities, actions, or rules give a policy its support and reinforcement in direction. Eg, a consistent company email signature, PCI-DSS, NIST, ISO etc. A standard is a more detailed statement of what must be done to comply with policy.
In the implementation of an inappropriate-use policy, the organization might create a standard that all inappropriate content will be blocked and then list the material that is considered inappropriate. Later in the process, technical controls and their associated procedures might block network access to such websites.
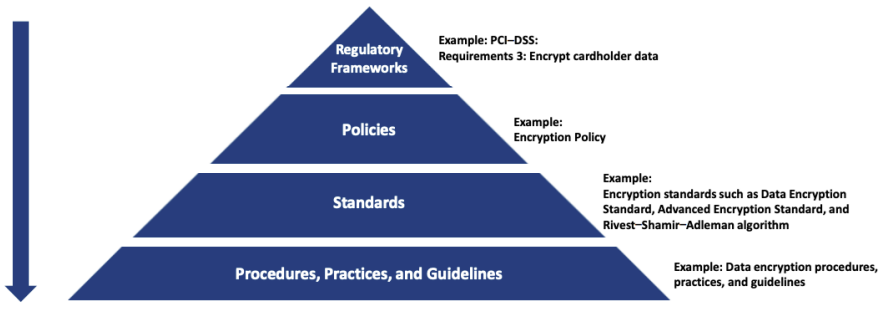
Baseline: A baseline sets a minimum level of security that all systems within an organization must meet. Systems not compliant with the baseline are typically taken out of production until they can be brought up to the baseline. Baselines are often established based on industry standards such as the Common Criteria (CC), Information Technology Security Evaluation and Criteria (ITSEC), or standards from organizations like the National Institute of Standards and Technology (NIST).
Guidelines: Guidelines offer recommended actions and guidance on applying specific standards or best practices. Unlike baselines, which are mandatory, guidelines provide recommendations on how to implement standards and baselines effectively.
Procedures: Procedures are step-by-step guides for accomplishing tasks related to cybersecurity. They describe the exact actions necessary to implement specific security mechanisms or solutions, such as hardware deployments. Procedures may follow established standards such as NIST, Cybersecurity Framework (CSF), ISO standards, or an organization’s internal standards.
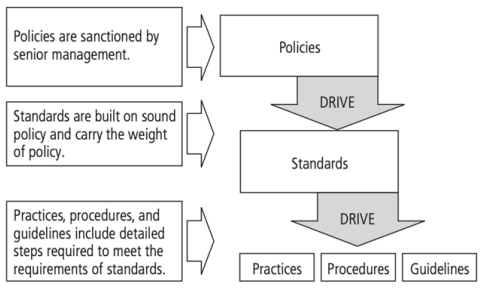
NIST Special Publication 800-14
Generally accepted system security principles
-
supports the mission of the organization
-
integral element of sound management
-
cost-effective
-
responsibilities and accountability should be made explicit
-
comprehensive and integrated approach: throughout entire information life cycle
-
periodically reassessed
-
constrained by societal factors
Types:
Organizations should have a structured approach to their information security policy framework:
-
Enterprise information security policy (EISP)
- Establishes the foundation of a Computer Security Program by clearly defining the scope, including which resources are covered - facilities, hardware, software, information, and personnel
- Sets the organizational strategic directions, such as defining program goals. For instance, for an organization handling large mission-critical databases, priorities might include reducing errors, data loss, corruption, and improving recovery processes.
- Assigns responsibilities within the organization for the implementation of computer security program and related tasks to other offices, such as Information Resources Management
- Addresses compliance requirements for establishing the program and delineates responsibilities. It also specifies penalties and disciplinary actions for non-compliance.
- Examples: Application policy, Network and network device policy, Backup and restore policy
-
Issue-specific security policies (ISSP)
- Focuses on topics of current relevance and concern, such as e-mail privacy or Internet connectivity, providing management’s stance on these issues.
- Requires more regular updates to reflect changes in technology, operational practices, or emerging security threats.
- Includes a clear issue statement outlining the organization’s position, applicability, roles and responsibilities, compliance requirements, and points of contact.
- Example: Remote access and wireless policies, incident response plan, password policies
-
System-specific security policies (SysSP)
- Centers around management’s decisions to protect specific systems, detailing the accountability measures for user actions within those systems.
- Ensures that policy decisions are made by a management official, based on a technical analysis of the system’s needs and security requirements.
- Acknowledges that security needs and policies will vary from system to system, depending on each system’s operational requirements, environment, and the manager’s risk tolerance.
- Policies are expressed as rules dictating who is authorized to perform specific actions (modify, delete, etc.) on particular classes and records of data, under defined conditions.
- Example: DMZ policy, encryption policy, intrusion detection and prevention, access control policy
This example illustrates the potential consequences of not following management-guided SysSP:
A new firewall administrator at Boom! Technologies, a defense contractor, applies firewall rules based on those from a previous employer, Open Idea University. While these rules were appropriate for an academic setting that valued the free flow of information, they fall short of the stringent security requirements needed for a defense contractor.
Security Audit
An audit is a systematic process designed to provide assurance and confidence to various stakeholders that an organization is operating within defined parameters, adhering to regulations, and managing its risks effectively.
-
Financial Audit:
- Focus: Ensuring that financial statements accurately represent the organization’s financial status.
- Stakeholders: Shareholders and potential investors.
-
Internal Audit:
- Focus: Evaluating whether internal controls are functioning effectively and risks are managed efficiently.
- Stakeholders: Management and the Board of Directors (BOD).
-
Statutory Audit:
- Focus: Confirming compliance with relevant legal and regulatory requirements.
- Stakeholders: Regulatory bodies and authorities.
-
IS (Information Systems) Audit:
- Focus: Assessing the security of IT assets, the efficiency of IT controls, and the minimization of threats.
- Stakeholders: Management and BOD.
IT Security Audit
-
Objective: To assess the security risks facing an organization and evaluate the effectiveness of controls or countermeasures in mitigating those risks. To evaluate the organization’s ability to protect its critical assets. - Ensures compliance with standards and laws. - Recommends improvements and enforces controls.
-
Scope: Involves a comprehensive assessment of the organization’s networked infrastructure, including computer systems, networks, operating systems, application software, etc.
-
Process: Conducted by auditors with technical and business knowledge of the company’s IT assets and business processes. The audit process includes interviewing key personnel, conducting vulnerability assessments and penetration testing, cataloging existing security policies and controls, and examining IT assets.
-
Methodology: Auditors utilize a blend of technology, manual efforts, and tools to perform the audit.
Areas:
- Data center facilities
- Networks
- System platforms
- Database
- Applications
Process:
-
Planning
- Objective: To establish the audit’s goals and scope.
- Activities:
- Conduct a risk assessment to evaluate risks and internal controls.
- Define specific audit goals.
- Develop audit checklists for systematic evaluation.
- Schedule the audit, calculating the necessary resources.
- Hold a kick-off meeting to discuss objectives, point of contact, and reporting mechanisms with the client
-
Fieldwork and Documentation
- Objective: To collect data, perform interviews, and analyze potential and existing risks.
- Activities:
- Apply the developed checklist to carry out audit procedures.
- Identify risks and weaknesses in internal controls, documenting these findings.
- Document working papers to support conclusions and learn from the audit process.
-
Issue Discovery and Validation
- Objective: To identify potential concerns and validate them with the customer.
- Activities:
- Report findings, especially those representing risky issues or lacking mitigative controls.
- Ensure timely reporting to correct issues promptly and avoid confusion.
-
Solution Development
- Objective: To develop an action plan for addressing identified issues.
- Approaches:
- Recommendation Approach: The auditor recommends solutions, which may not always be implemented effectively.
- Management-Response Approach: The auditor reports issues (with or without recommendations) and asks for management’s response.
- Solution Approach: Both the client and auditor mutually agree on an action plan.
-
Report Drafting and Issuance
- Objective: To create and distribute the audit report.
- Components:
- A statement of audit scope detailing the areas covered.
- An executive summary highlighting major issues and the action plan.
- A detailed list of issues and proposed action plans, written in layman’s terms.
- The audit conclusion, categorizing the audit outcome as satisfactory, unsatisfactory, or needing improvement.
-
Issue Tracking
- Objective: To monitor and ensure the resolution of audit points.
- Activities:
- Track and follow up on issues until they are fully resolved.
- Escalate unresolved issues as a final resort.
- Validate the resolution of issues, such as through testing a Business Continuity Plan (BCP).
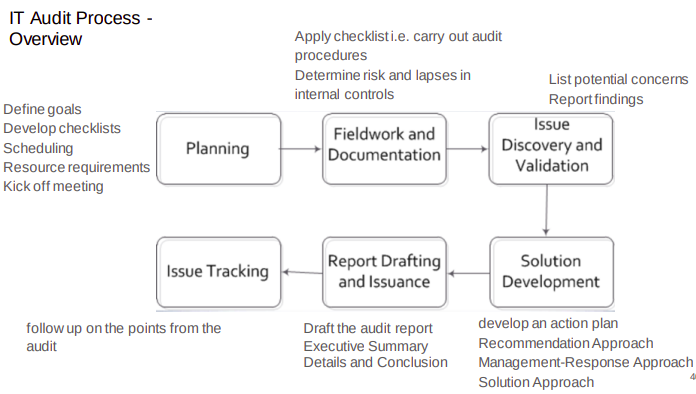
Ethical Considerations
For information security (IS) professionals, navigating the complex landscape of legal and ethical responsibilities is critical to safeguarding an organization’s assets and reputation. The legal environment related to information security is constantly evolving, with new regulations, standards, and challenges emerging regularly.
-
IS professionals must have a deep understanding of the current laws and regulations that affect information security. This includes
- data protection laws (such as GDPR in Europe, CCPA in California),
- cybercrime legislation,
- intellectual property laws, and
- industry-specific regulations (like HIPAA for healthcare in the USE)
-
For organizations operating internationally, IS professionals should understand legal obligations not just in their home country but across all jurisdictions where the organization conducts business.
ignorantia Juris Non Excusat
The legal principle “ignorantia juris non excusat” or “ignorance of the law excuses not” underscores a foundational concept in many legal systems worldwide. It posits that a person who is unaware of a law may not escape liability for violating that law merely because of their ignorance. This principle ensures the law’s efficacy and enforces the idea that citizens are responsible for knowing the law.
- Prevents individuals from using ignorance as a defense against liability
- Emphasizes the importance of legal awareness and encourages individuals and organizations to educate themselves about the laws relevant to their actions and operations
- Reinforces the idea that laws are to be followed and that knowing and understanding legal obligations is a responsibility of individuals and entities alike.
Examples:
- Several companies have faced significant fines for failing to comply with the GDPR, often due to a lack of understanding of the regulation’s requirements.
- Cases where businesses used copyrighted images or software without permission or proper licensing illustrate the principle.
Cybercrime and cyberterrorism
Cybercrime is primarily driven by the desire for personal gain. This can include financial profit, access to confidential data, or personal revenge against individuals or organizations.
- Hacking
- Phishing
- Fraud and identity theft
- Ransomware
The impact of cybercrime can be substantial, resulting in financial losses, breaches of privacy, and reputational damage to victims. However, the primary aim is not to induce fear or influence policy but to benefit the perpetrator(s) financially or personally.
Cyberterrorism is driven by ideological or political objectives. It aims to spread propaganda, disrupt critical infrastructure, or incite violence, with the goal of influencing government policies or societal norms.
- DoS
- Sabotage
- Espionage
Unlike cybercrime, the consequences of cyberterrorism can extend beyond financial loss or data breaches. It can lead to physical harm, social unrest, or national security threats.
Laws and Ethics
Laws are formal rules and regulations that are adopted and enforced by governments. They are designed to codify expected behaviors and establish standards for conduct within society.
- Codification: written and recorded statutes that provide clear guidelines on what is permissible and what is not
- Enforcement: government enforce laws through judicial and regulatory mechanisms
- Objectivity: laws are meant to be applied universally within a jurisdiction, regardless of an individual’s beliefs
Ethics refer to the socially acceptable behaviors that conform to the widely held principles of the members of a society. They are the moral standards that guide individuals on what is considered right or wrong
- Social acceptance: derived from norms and values
- Flexibility: varies across cultures and societies
- Moral guidance: as a moral compass for individuals
Systems of laws: civil, common, religious
Types of laws: criminal, civil, and administrative
Civil law and criminal law represent two fundamental branches of the legal system, each with distinct processes, objectives, and standards of proof.
| Aspect | Criminal Law | Civil Law |
|---|---|---|
| Purpose | To deal with crimes and legal punishment of criminal offenses. | To resolve disputes between parties and provide compensation to the victim. |
| Standard of Proof | Beyond a reasonable doubt. | Preponderance of the evidence (greater than 50% chance the claim is true). |
| Burden of Proof | Always on the state/government. | Falls on the plaintiff. |
| Common Disputes/Offenses | Theft, assault, robbery, trafficking in controlled substances, murder. | Landlord/tenant disputes, divorce, child custody, property disputes, personal injury. |
| Outcomes | Punishment such as incarceration, fines, community service, or probation. | Compensation for injuries or damages, disposition of property. |
| Focus | Punishing the offender and deterring future crimes. | Remedying harm to the aggrieved party. |
| Examples | Computer Fraud and Abuse Act: Addresses unauthorized access, fraud, and damage, related to federal computer systems. | Privacy Act of 1974: Protects personal information held by the Government. |
| HIPAA: Privacy of personal medical records |
Privacy in USA vs EU
USA:
- 4th Amendment: the basis for privacy rights
- Privacy Act: limits the ability of federal government agencies to disclose private information without prior written consent of the affected individuals
- Electronic Communications Privacy Act (EPCA): makes it a crime to invade the electronic privacy of an individual
- Comm Assistance for Law Enforcement Act (CALEA): ammendsECPA
- Identity Theft and Assumption Deterrence Act: makes identity theft a crime against the person
- Health Insurance Portability and Accountability Act (HIPAA): privacy and security regulations requiring strict security measures for hospitals, physicians, insurance companies
- Health Information Technology for Economic and Clinical Health Act (HITECH): updates many of HIPAA’s privacy and security requirements organizations that handle protected health information on behalf of HIPAA covered entity.
- Patriot Act: uniting and strengthening by providing appropriate tools to intercept and obstruct terrorism (in response to 9/11)
EU:
- European Union Privacy Law
- Privacy Shield
- GDPR: comprehensive law covering the protection of personal information
Ethical Hacking and Responsible Disclosure
Ethical hacking involves the practice of deliberately probing a system, network, or application for vulnerabilities, but with a crucial difference from malicious hacking: it is done with the explicit permission of the system’s owner. The primary goal is to identify and rectify security weaknesses before they can be exploited by malicious actors.
Ethical hackers are typically well-versed in the art of cyberattack methods, with a deep understanding of how to identify and exploit system vulnerabilities. However, they use these skills to improve security rather than to breach it.
- Consent: Ethical hackers must always obtain explicit permission from the system owner before conducting any tests. This consent serves as a legal and ethical foundation for all activities undertaken.
- Privacy: Ethical hackers must respect and protect the confidentiality of any data encountered during their assessments.
- Responsible disclosure: Upon discovering vulnerabilities, ethical hackers are faced with the responsibility of how and when to disclose these findings. The goal is to protect users while providing organizations the chance to remediate flaws.
- Potential for misuse: There is a constant risk that the knowledge and tools used by ethical hackers could be misused, either by the ethical hackers themselves turning rogue or by their methods being replicated by malicious parties.
- Integrity and responsibility: - Ethical hackers must conduct their activities with the utmost integrity and responsibility, ensuring that their work genuinely contributes to enhancing cybersecurity.
Deterring unethical and illegal behavior:
Deterring unethical and illegal acts within an organization involves a multifaceted approach that leverages policy, education, training, and technology.
-
Ignorance: ignorance of the law is no excuse, but ignorance of policies and procedures is - education, policy dissemination, ongoing training
-
Accident: mistakes of high authorized individuals - implementation of controls
-
Intent: some people like to watch world burn - legal and technical deterrents
Laws and policies and their associated penalties only deter if three conditions are present:
- Fear of penalty
- Probability of being caught
- Probability of penalty being administered
Organizations for code of conduct of IS professionals:
-
SANS: Provides training and certifications (Global Information Assurance Certification - GIAC) for security professionals. Emphasizes respect for the public, the integrity of the certification, employers, and oneself.
-
ISACA: Offers certifications like CISA, CISM, and promotes the effective management of IT governance and risk. Encourages compliance with standards, professional care, honesty, and maintaining confidentiality.
-
(ISC)^2: Known for the CISSP certification among others, focusing on information security leadership and operations. Members must protect society and the infrastructure, act honorably and legally, provide diligent service, and advance the profession.
Cyber Law in Nepal
The Electronic Transaction Act 2063 (2008) of Nepal encompasses a wide range of areas crucial to the governance and regulation of electronic transactions, ensuring the security and integrity of digital interactions. This Act is pivotal for addressing the challenges and threats posed by the digital age, including computer crimes, ensuring privacy and data protection, and establishing standards for digital signatures.
Additionally, the Nepal Rastra Bank’s (NRB) IT Guidelines complement the Act by mandating annual IT audits, designating a senior official as the Information Security Officer, emphasizing data security, and more, to fortify the financial sector against digital threats.
- IT strategy, policy and procedures
- Senior official to be information security officer
- IT audit manually
- Mobile and ATM protection
- Data security
- Outsourcing
- BCP
The Act categorizes various offenses related to computer and information systems, detailing specific punishments for each. These offenses and their corresponding penalties include:
-
Five-year imprisonment for illegal publications
- Illegal electronic publications
-
Three year imprisonment group
- Privacy/destruction/alteration of code
- Unauthorized access
- Damage to computer systems
-
Two-year groups with varied fines
- Breach of confidentiality (10k)
- False statements/licenses/certificates (100k)
- Computer fraud (100k)
-
Six-months to half penalty group
- Abetment in offenses
- Accompliance liability
-
Special considerations
- Offsenses committed outside Nepal are also punishable
(not sure where to put this shit)